
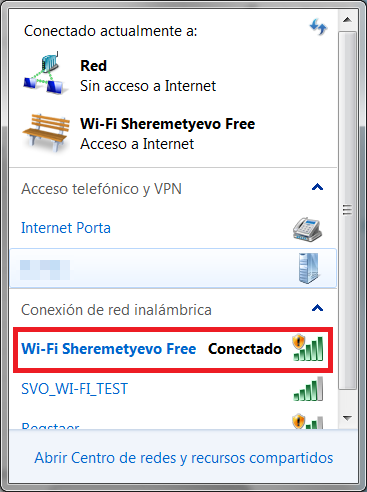
As most travelers know, many airports and VIP lounges offer Wi-Fi connectivity but, unfortunately, these connection are rarely encrypted. Here’s an example:
All data sent and received travels in clear text, which means anyone could intercept the data for malicious purposes. This unencrypted data could include passwords, logins, financial information like PIN codes, etc.
Many people also know that it’s always better to use a VPN connection. However, in many cases, VPN connection are filtered out and blocked by rules on the network firewall. I tried two different protocols and both were blocked. Mostly network administrators don’t allow using VPNs from Public WiFi access points only because they want to make sure the network isn’t be used for malicious purposes without any readable network logs. These policies actually allow to the bad guys to launch really easy man-in-the-middle attacks when all traffic pass through a malicious host.
The reality is that using a public Wi-Fi service can expose your really sensitive data to cybercriminals. Recently, we saw some famous people lose their Facebook and other social network passwords by using open (insecure) Wi-Fi connections.
So what is the solution when your VPN is blocked? Well, in some cases, an SSL (https) connection may help. Please, before going to any Website, type in the address bar https:// and then the domain name. After the page is loaded, please check if the certificate used for encryption is a valid one and issued to the site you’re visiting. If you see something wrong with the certificate, stop using the site.
Another solution is to use a cable Ethernetconnection instead of a WiFi. Many lounges have such connection as well; it will be much safer for
you.
In any case if you’re connected from a public place, it’s better not to use eBanking or ePayment services. That data is the main target for criminals. So, travel safe and keep your personal data safe as well!






















WiFi + Airport = Lost password