
How much money and effort does it take to become a good reverse engineer? Do you even need to be one?
There are no universally acceptable answers to these questions. Software reverse engineering (RE) is not a science but a skillset combined with specific knowledge and backed by a lot of experience.
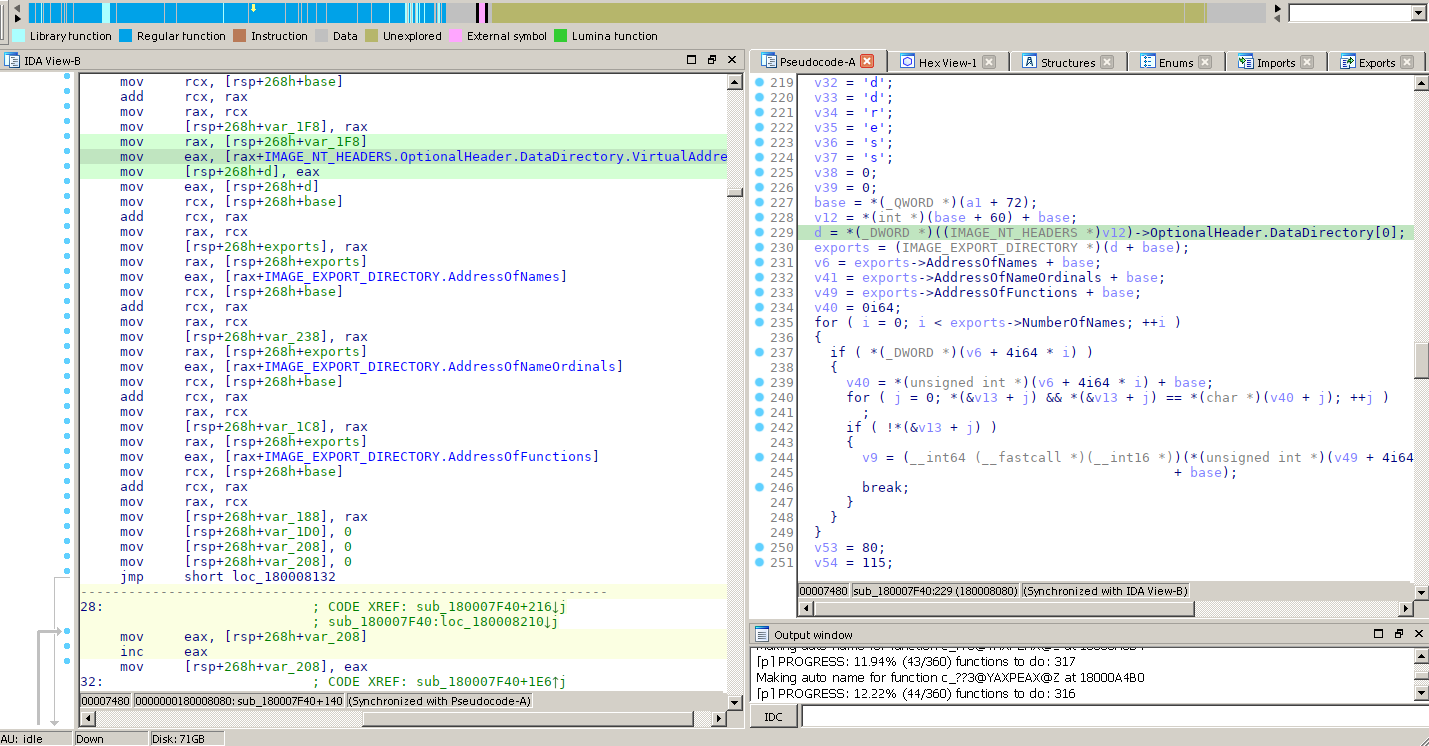
For several years, we have been sharing the RE knowledge that we accumulated in the form of training sessions provided to paying customers. These sessions took from two days at the SAS conference to complete five workdays in the extended version, and covered many aspects of our own work, primarily in IDA Pro and the in-lab reverse-engineering framework.
Due to the novel 2019 coronavirus disease, our schedule for the training sessions has changed completely. But not only this; the reversing landscape itself has changed since last year. Released in March 2019, the free and open-source reverse engineering tool called Ghidra lowered the barrier to entry into the field.
So, while we are all working from home and, hopefully, have time to learn something new, why not tear some binary code apart and pick up some reverse engineering skills? This may prove especially helpful if your work is related to malware, incident response or forensics.
It is certainly not feasible to learn RE in one webinar. Within one hour, we will outline the typical workflow that we follow when analyzing malware. We will dissect real-life malicious code using both IDA Pro and Ghidra, and use some of the most useful features of these disassemblers.
The rest, as in many other disciplines, comes with experience. And, we are still looking forward to seeing you in our reverse engineering training sessions at SAS Conference 2020 (two days) or elsewhere (a whole week!).

What does it take to become a good reverse engineer?




















Dim
hi guys, any plans for APAC timezones?
Abdul Hameed Oluwashegu Tade
Need a mentor in reverse engineering. Anyone willing to help ?
elroy
Learn CPU/OS internals, C/C++ and ASM, master tools like IDA Pro and Ghidra, and practice on real binaries—reverse-engineering skill comes mainly from hands-on experience.