
Where is my tax refund? Wait! What are that fraud charges on my credit card??
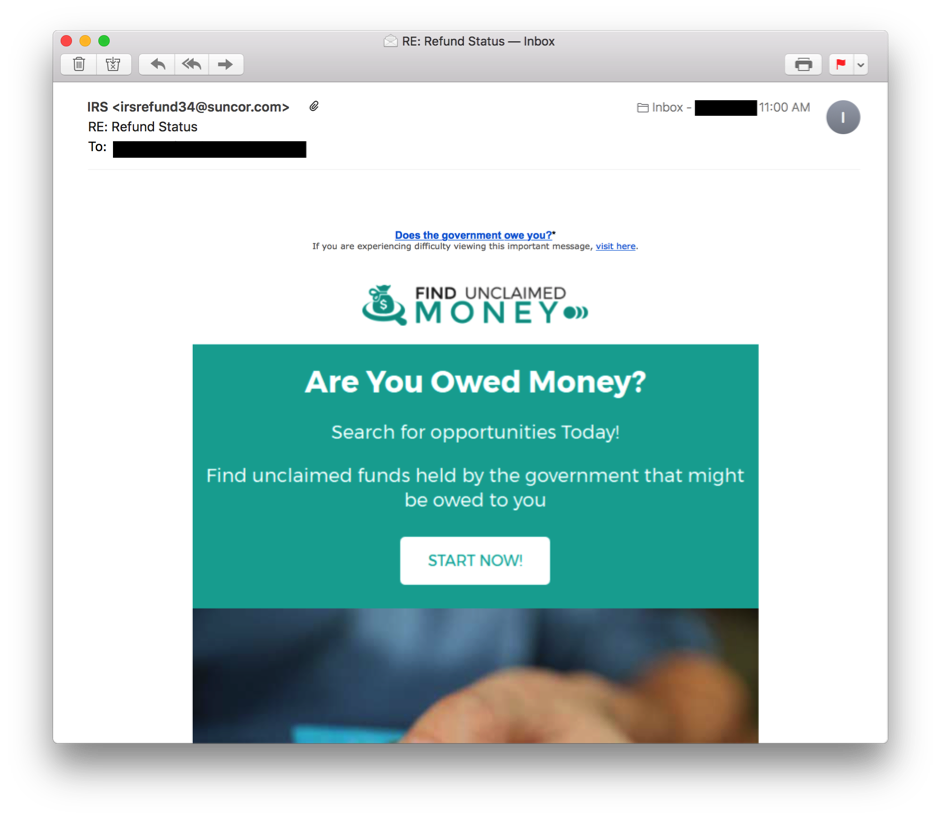
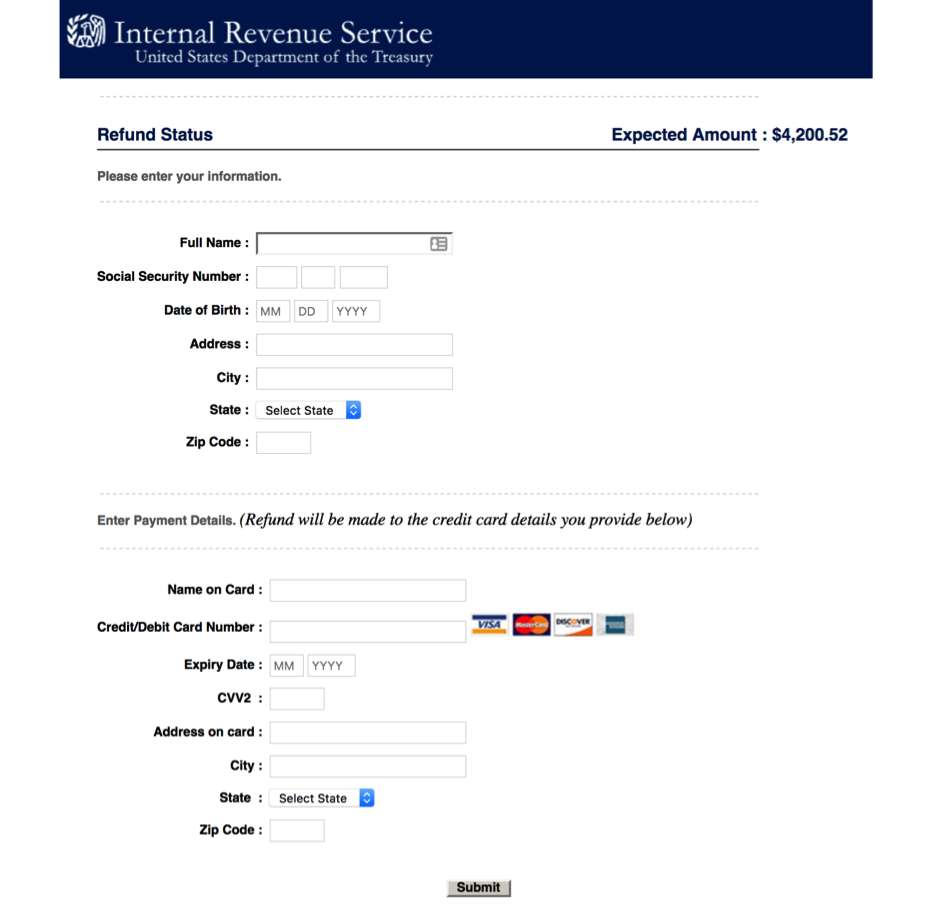
On Monday, Jan 29th, IRS officially opened its 2018 season. Some taxpayers already filed their taxes and cybercriminals know it too. So, right after two days of the official 2018 season opening, we got phishing messages with a fake refund status Websites:
The link in the email leads to a hacked Brazilian restaurant, redirecting to Website with Australian domain zone.
So, the whole scheme is to steal credit card information of the taxpayers expecting a tax refund from IRS. Both URLs are blocked by Kaspersky Anti-Phishing now.
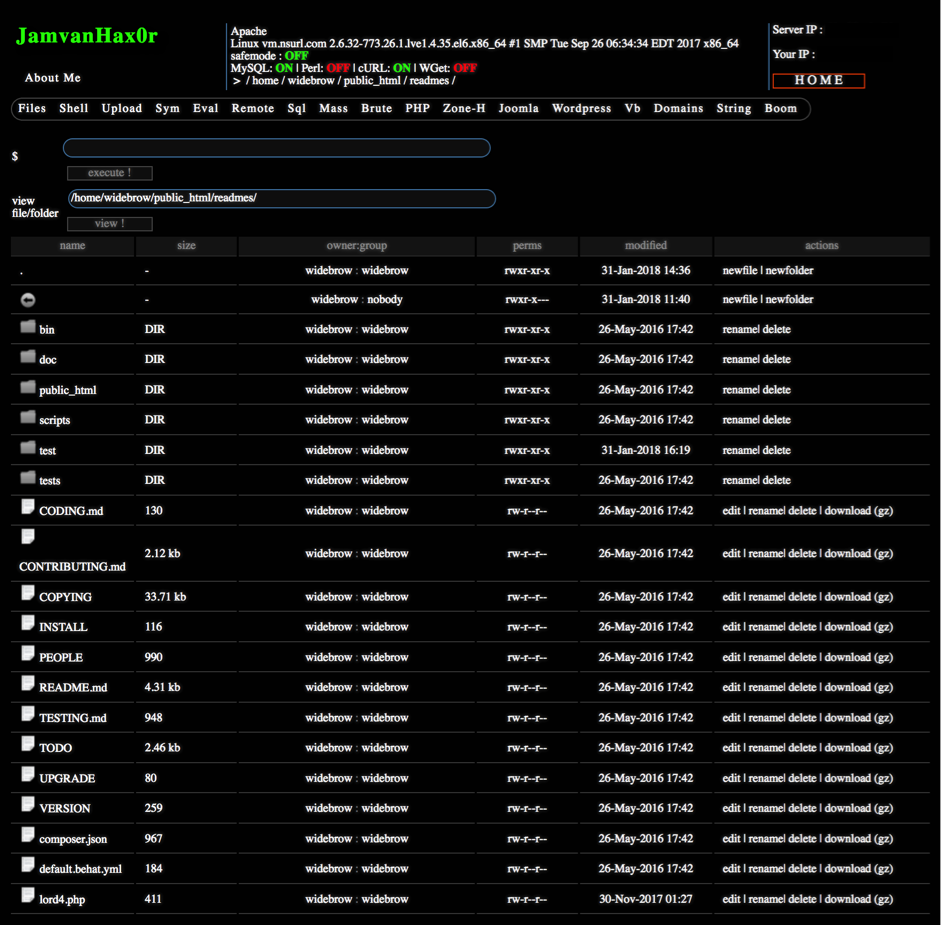
The mentioned website was hacked and includes an old Webshell uploaded back to 2016. The server has directory listing enabled.
Should we expect more campaigns like this? Definitely yes. Stay watchful and don’t lose your refunds!
Cybercriminals target early IRS 2018 refunds now






















Mohamed
Can you please share IOC ?