
At the moment I’m in Johannesburg, South Africa, talking at the opening of our local office about security and mitigation strategies.
Despite being a booming city, Johannesburg, tribute to its distant location from the information centers of the world, has remained somehow behind others in terms of internet connectivity. This may change very soon, though.
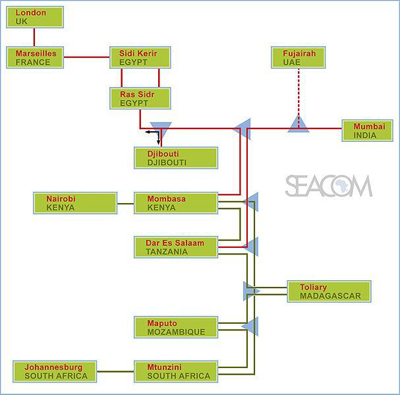
Source: Seacom HQ c/o Linda Carter
Meet Seacom. Seacom is a fiber optic network which connects a large part of the African continent with UK, France, Egypt, UAE and India. One of the interesting issues raised by some of the journalists during the past days is the link between cybercrime and Seacom.
A long time ago, when people used 2400bps modems (do you still remember those?), one could pretty much “hear” where there was something odd going on, for instance, a hacking attempt, with their machine. Similarly, there used to be a time when I could tell if a computer was infected by just listening to the sound of the hard drive spinning while executing a clean file. Nowadays, with fiber optic and SSD drives, such things are but long forgotten stories. Over a regular fiber optic link, it can take less than a few minutes to transfer one full GB of confidential information from a compromised machine. Or, it might take a few microseconds to inject a backdoor into an unpatched Windows machine.
It is hard to predict if there will be a major raise in cybercrime in South Africa in the very near future due to Seacom. Yet, one needs to keen in mind what increased bandwidth brings:
- P2P applications, file sharing and exchange
- Illegal music and movie downloads
- Pirate software
While these are not necessarily directly connected to cybercrime, a vast amount of pirate software nowadays contains trojans, both for the PC and Mac. Similarly, leaks caused by P2P applications are known to have caused serious incidents all around the globe.
Spam is another problem. Even the network attacks, which have decreased in amount during the recent years, seem to benefit from increased bandwidth.
What about mitigation? As usual, prevention is better than the cure. I’ve compiled a short list of security tips that I constantly recommend in my presentations:
- Install and run an Internet Security Suite
- Don’t assume a website is safe because it is high profile
- Use an up-to-date, modern browser: IE8, FF 3.x, Chrome, Opera 10
- Keep Windows up-to-date
- Always run the latest versions of Adobe Reader, Flash Player, MS Word, etc…
- Be wary of messages from social networks
There are a lot of good things that increased bandwidth will bring, just make sure you’re not going to fall victim to its unwanted side effects.





















The link between high speed and cybercrime