
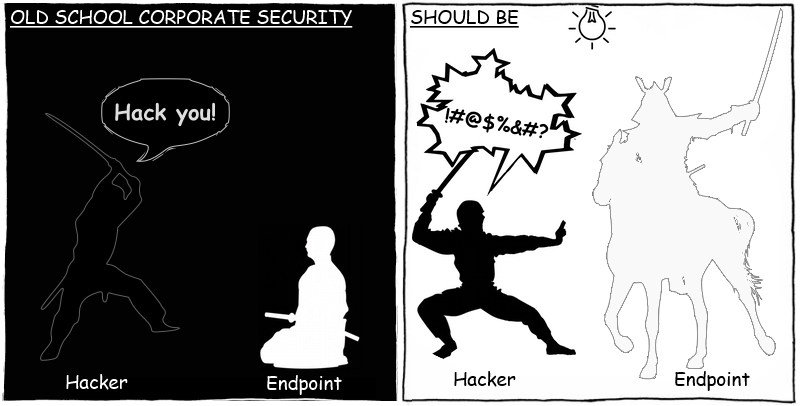
The experience of many information security officers shows that only a small portion of security incidents take place as a result of meticulously planned and sophisticated targeted attacks, while most incidents are due to a lack of effective security and control measures. This post begins a series of publications about IT security threats associated with the use of legitimate software.
TeamViewer
Hugely popular, easy-to-use and practical, remote access tools have been appreciated by system administrators and developers alike, as well as by anyone who has ever needed to log on to a work computer from a remote location, whether traveling on business, working from home, or caught out by an emergency while on vacation. However, unregulated use of this software poses a threat to corporate security and may lead to security incidents.
For example, TeamViewer, a relatively widespread remote access tool, was used for spying in Eastern Europe, targeting both state-owned and privately-held companies. However, using remote access software to intrude into a corporate network is potentially more than an external threat (involving cybercriminal activity and malware). Internal threats can be every bit as significant: corporate employees can potentially abuse remote access with software being installed and used by an insider for malicious purposes.
Let us look at some of the potential threats with a real-life case study by Kaspersky Lab’s experts.
Case study. A real-life story
In a large software company, an employee often worked long hours. He regularly went to the office on weekends to meet his deadlines. Tired of such a demanding routine, he followed his colleagues’ advice and installed TeamViewer. Now, he did not have to work extra hours in the office or come in on weekends: he could work from home, remotely accessing his work computer.
TeamViewer made life easier for that employee, but it made things difficult for the IT security officer in the same company. Before long, the security officer noticed that there were more incidents occurring on the corporate network: the antivirus product began to detect more malware, there were increasingly frequent attempts to access confidential data without authorization, etc. A brief analysis showed that most of the malicious activity was associated with the computer of just one user.
An in-depth security scan of the suspicious computer did not reveal any malware. The security officer suspected that a colleague may have accessed the employee’s account and used it to conceal his/her criminal activity. However, when he analyzed the data from the entrance gate and the CCTV surveillance, he discovered that no one had been in the office at the times the activity was taking place. There was one other possibility: an undetected backdoor might be present on the affected computer. An analysis of network traffic revealed that the security incidents took place at the same time as surges of network activity on the same computer. Although the traffic via ports 80 and 443 was encrypted, it was established that the traffic communicated with servers with domains such as ‘serverXXX.teamviewer.com’.
An examination of the suspect computer revealed a TeamViewer server running on it. The security officer conducted an interview with the employee, and found out about the remote access to the corporate network was used, but the employee stressed that he had not been connected to the corporate network when the security incidents were occurring.
An inspection of the employee’s home computer showed that some time ago a spyware program had been detected and removed. The employee did not give it much further thought, since his security product had successfully neutralized the threat. A detailed analysis showed that the spyware program was designed to log information typed from the keyboard, and capture areas of the screen.
The IT security service concluded that a spyware program installed on the employee’s home computer had transmitted to a cybercriminal the data required to access the office workstation.
With this information, the malicious user gained entry to the corporate network, scanned it, installed malware, searched for vulnerabilities and tried to copy files from network resources.
Fortunately, the malicious activity was quickly terminated thanks to the IT security staff’s timely actions, and the cybercriminal inflicted only limited damage. The employee responsible was reprimanded, while the chief security officer called for prompt action to be taken so as to preclude similar incidents from happening in the future.
Solution
One important step in processing security incidents is to correct the defects in the corporate security policy that made the incident(s) possible. So, what should an IT security officer do in this case?
Primary analysis
When a security incident is detected, an IT officer’s first task is to find out if the incident was isolated, or if it could potentially re-occur on other computers in the network. A software inventory enables officers to collect information about all software installed on users’ computers, while software monitoring will help find out how often it is used. A basic analysis will supply the IT security officer with, among other things, a general picture of how remote access software is used in the network, who uses it, and how often.
Network traffic control
Inadequate control over connections made to the corporate network is one source of security incidents. The most appropriate tool to control network connections is a firewall, while there is IPS for controlling network traffic. However, while the tools controlling the corporate network perimeter are important, they had only a limited effect in the case described above. One TeamViewer client established a connection to another via remote servers, while data in the form of encrypted HTTP packets can be communicated via ports 80 and 443. It is not feasible to block all such traffic, as this would bring work to a complete standstill. On the other hand, blocking connections to all the domains or IP addresses of TeamViewer servers entails a lot of work. It requires all related domain names and IP addresses to be identified, and those lists must subsequently be kept up to date.
Application control
Application control is evidently an appropriate tool to reduce the risks of intrusion into a corporate network via TeamViewer as it can place curbs on its uncontrolled use.
With application control, an IT security officer can address two problems:
- Control over TeamViewer use.
- Restricting TeamViewer access and capabilities to reduce the possibility of cybercriminal intrusion.
TeamViewer is a convenient tool. For instance, it enables administrators to assist users regardless of where the system administrator is physically located. The use of TeamViewer (or a secure alternative) can be permitted to those users who really need remote access. For all other employees, any capability to launch any remote access software should be disabled.
This decision seems complex on the face of it: the searching, compiling and maintaining a complete, up-to-date list of all remote access software programs takes time and effort. However, the use of application control in Default Deny mode solves the problem of maintaining and updating lists of unauthorized software.
Once those who do not need TeamViewer are dealt with, an IT security officer’s task is simplified to controlling a select group of employees who are in the risk zone.
Let us assume an employee has the rights and permissions to use TeamViewer, but a cybercriminal manages to steal his/her connection credentials. How can the potential damage be minimized?
Apart from blocking certain activities, application control enables the security officer to restrict the application’s capabilities by applying HIPS policies, such as restricting access to network resources, restricting privileges to launch and/or load applications, disabling any changes in configurations, etc. This will help to restrict TeamViewer’s capabilities as much as is practical, should it be used by a cybercriminal.
Security Policies
Although Teamviewer has an extensive list of functional capabilities, it does not include any tools for the administrator to exercise centralized control in a corporate network. Certain settings in TeamViewer help reduce the risk of intrusion; these include the generation of a new connection password when TeamViewer is launched; the option of restricting the list of ID clients for which connection is allowed; and establishing a VPN connection between two TeamViewer clients. However, it is the user who decides whether specific restrictions are used or not. Naturally, the administrator can install and configure TeamViewer, and password-protect it against any changes in settings. However, it makes no sense to try to impose control over any changes to the settings, since users can run a portable version brought in on a USB drive.
All employees must be aware of corporate security policies. One of the IT security officer’s tasks is to hold regular security briefings for employees and ensure existing policies are pursued. For instance, users should:
- Launch TeamViewer with minimum privileges, with no possibility for increased privileges;
- Generate a new key at each launch;
- Use TeamViewer only when needed; not leave it running unattended;
- Not store connection credentials or pass them to others in an unencrypted form;
- Immediately inform corporate IT security if a cyber attack is suspected.
Conclusion
From an IT security standpoint, remote access software risks compromising the corporate network perimeter. This is the case both when the software is used in an uncontrolled way, and when security regulation is neglected while connecting to a corporate network from outside. The network activity of the software greatly complicates the identification of malicious activity against the backdrop of legitimate activity. Detected use of remote access software without IT security’s prior approval may even be considered sufficient evidence of an intrusion by a cybercriminal.
To minimize the risks of such security incidents taking place, remote access software must be restricted as far as possible; this can be done with the help of application control. When employees have to use such software for business purposes, every effort must be taken to minimize the risk of a cyber attack. Establishing HIPS policies, launching with minimum privileges, mandatory domain authorization, preferably in two stages – all of these will help reduce the risks of using potentially hazardous software to an acceptable level.
Security policies: remote access programs






















Amjad
Awesome
Prasanta Shee
TeamViewer is good but its data has been recently hacked. Have a look at http://www.bbc.com/news/technology-36459015 Are hosted services secured? Why not use on premise remote support solutions like R-HUB remote support servers? It works from behind your corporate firewall, hence better security.