
Everyone has their own preferences in choosing applications: a favorite browser or instant messenger, media player or email client, etc. Many users are so accustomed to them in everyday life that they feel uncomfortable without access to their favorite programs at work or in college. As a result, they come to use the portable applications which we will discuss in this article.
Portable applications, stored on removable media, are very convenient: they need no installation and can be used in almost any environment. For users, this means their favorite tools are always at hand, and ready to do anything from playing movies and music to analyzing and restoring the system.
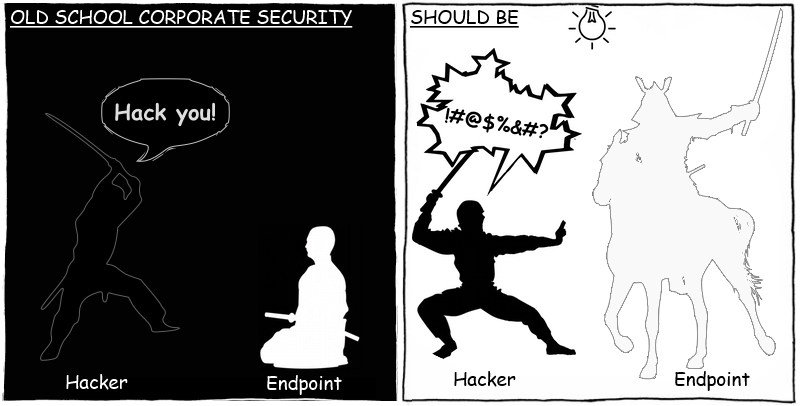
However, such applications can also pose a threat to information security. Users who do not have local administrator rights cannot install software on the PC, but they can bypass this restriction by taking advantage of portable applications that do not require installation. Since these applications are mobile and are stored on removable media, they often go undetected by auditing applications on the LAN. This makes it more difficult to investigate incidents related to the use of portable applications as the information about removable media and software installed on it is often unavailable to the IT security specialists.
Case study
An analytical company engaged in processing large amounts of personal information offered part-time work to students and non-IT-specialists: a couple of days a week they would transfer data from paper into electronic forms, recheck the available data for errors and contact people for further information.
For security reasons, all workstations used by these employees were integrated in a separate subnet with no access to the internet. One of the company’s system administrators was put in charge of this park of PCs.
The company commissioned third-party programmers to develop software for these e-forms. The program represented a catalog of various e-forms identical to their paper counterparts. To monitor the work, every temporary employee had to enter a username and password at startup. Then they chose to fill in a new e-form or check a previously filled one. Both new and modified data was saved in an intermediate database. In order to extract the data to be checked and updated, the program sent a request to the intermediate base which, in turn, received the data directly from the main database. To prevent the employees from checking the same form again and again, a restriction was introduced to the intermediate base: forms could only be accessed 5 months after they were last revised. The database administrator was put in charge of creating and maintaining both databases.
The workflow was simple enough and the staff turnover was high so the system administrator took measures to secure the workplaces: all users had minimal necessary rights, could neither install new software nor change the settings, and only had access to the server on which the intermediate database was stored. At the first sign of any problem with any PC, the administrator immediately restored the system in full from a reference copy.
It was all going well until the intermediate database started failing regularly, seriously complicating the work of the temporary employees. While analyzing the roots of this instability, the DBA noticed a lot of recently accumulated error messages. These errors were mostly caused by a high load on the database due to the large number of requests sent to the database. However some errors were caused by the attempts to read/write the data in tables where access was forbidden. The administrator discovered that all the database requests which generated errors had been sent on behalf of the program for filling e-forms.
After talking to the program developers, the DBA realized that this behavior had not been integrated in the program, nor it could have been caused by a bug in the code. The DBA enabled detailed logging of events and saw that all abnormal requests had been sent from a single IP address. He turned to the system administrator for help, and without thinking twice the sysadmin restored the system from the reference copy as usual.
Over the next couple of days, the database remained unstable and the users continued complaining. An analysis of the suspicious PC conducted by the system administrator did not detect any viruses or third party software or configuration changes. Discussions between the system administrator and the PC’s users led nowhere – none of them had noticed anything strange when working with the system.
Later, the DBA informed the system administrator that there were more error sources: now the errors were associated with different IP addresses on different days. Then the system administrator enabled detailed logging of events on all systems. This found a record of an error which caused a program failure on disk “F: ” on one of the systems. However, all computers in this network had only one hard drive which was listed in the system as “C: “. The system administrator suspected that someone from the temporary staff was deliberately trying to manipulate the database using software brought on a flash drive.
Having compared the times when the errors occurred and the IP addresses of suspicious PC users who were working those shifts, the administrator could find the alleged scammer. Then, during a “snap” inspection carried out during working hours, one of the students was caught and a flash drive was seized from the computer on which he was working. The flash drive contained portable programs: a disassembler and a utility to connect to the database. The student described how he had studied the program for filling e-forms with the help of the disassembler and how he had found the credentials necessary to access the database in its code. He also said that he had tried but was unable to access to the main database. Then he decided to copy more personal information (names, addresses, phone numbers and email addresses) in order to sell it to spammers. To automate the process, he wrote the script which sent requests to the database in loops. This explained the high load on the database and its subsequent instability.
The fraudster managed to sell a large amount of personal data to third parties. The damage to the company was significant. The student was not only fired but faced criminal prosecution. The head of the IT department and the system administrator were reprimanded and handed a financial penalty. The company’s management started considering the need to invite industry professionals to ensure information security for both the company as a whole and the processing of personal data in particular.
Solution
Although the company had taken measures to ensure security, they proved to be insufficient. It is important to note that these measures were aimed at preventing a direct threat, for example fraudulent intrusion from the dedicated subnet to the corporate network. As a result, the company remained vulnerable to indirect threats. Thus, the leak of personal data was the result of a combination of factors: failure to address the possibility that removable media and portable applications might be used, the allocation of unencrypted data to access the database in the program code, and the lack of control over access to personal information. Of course, it is not always possible to completely eliminate such factors but controlling them can definitely reduce the potential risk.
Device control
The first obvious problem in this case was the use of the USB devices by employees whose work did not require them. Based on the tasks described in this case, temporary staff needed only a mouse, a monitor and a keyboard. The more reliable solution here would have been to seal and enclose the system unit in a metal box and keep it under lock and key (as with an ATM or public terminal). That would guarantee maximum security, but would make servicing much more complicated.
On the other hand, device control in combination with other control mechanisms can ensure the desired protection level. The advantage of this approach is its flexibility: the system administrator can centrally manage policies to determine which devices are allowed to be used, as well as by whom and on what PCs. Another important advantage of this software is a log and audit of events. This information can be very helpful if there is any incident to be investigated.
Application control
As mentioned previously, control over one device is not enough. Apart from USB connections, scammers could use FireWire, CD / DVD, network devices (including which connect directly to the Internet) or the COM port.
Application Control is a tool that allows even non-IT specialists to provide adequate security. In particular, with reference to the events described above, blocking the launch of applications from removable media have proved a simple and effective means of protection from both portable applications and malware. In addition, application control is essential for the safety of “isolated” systems and networks (computer classes) – the “default deny” mode simply does not allow the users to run any third party programs. Moreover, the event audit part of the application control system can provide a detailed analysis of the incidents.
Encryption
It is often impossible to completely ban the use of removable media, especially when they are integrated in business processes. In such cases, the balance between security and flexibility can be achieved by ensuring the protection of those business processes. In particular, full data encryption on corporate removable storage media prevents the use of these devices outside the corporate network – writing and reading is only possible on the company’s computers while the use of all other devices may be blocked by device control. As a result, encrypting removable drives and hard disks reduces the risk not only of accidental data leaks (in case of the device loss) but also of deliberate data theft.
Security policies
Readers will already have noticed that the key flaw in the case above was bad organization: the system administrator was supposed to be responsible for information security, the third-party program was not tested for compliance with security regulations, there was no approved procedure for handling incidents, etc.
The incident showed that the security measures taken by the system administrator not only proved to be ineffective against indirect threats but were prompted by a false sense of security. In large companies, IT specialists develop both administrative security policies and specific recommendations for system administrators (to configure the company’s servers and workstations), for software developers (software requirements in terms of information security), for HR (procedures for hiring and firing employees), etc.
In small companies system administrators have to deal with these problems on their own, which obviously affects the effectiveness of information security. If there are no resources for the organization of a fully-fledged IT department, it’s important to consider automating the means of controlling and auditing information security. When choosing security software, attention should be paid to the full cost of ownership, i.e. the cost of buying, deploying and maintaining the solution – very often only trained professionals can effectively use sophisticated security systems.
Conclusion
Portable applications have made the life of the ordinary user much easier: your favorite apps are at hand anytime, anywhere. However, this mobility makes security protection even more complicated, especially controlling software use and investigating incidents.
The above story leads to the simple conclusion: ignoring information security jeopardizes not only a company’s business – it can also cause serious problems for its customers. This is why the in many countries legislation requires that organizations engaged in the storage and processing of medical, financial and other personal data follow international safety standards such as HIPAA, PCIDSS and many others. After all, the companies are responsible to their customers for the security of their personal information – its confidentiality, availability and integrity.




















Security policies: portable applications