
Here’s an unusual spam message that turned up today:
If it wasn’t for the official name at the top of the message, you could almost be forgiven for thinking it was just another real estate advert… “Fully furnished. Situated close to retail outlets. Excellent access to public transport and local schools. Contact US Department of Defense for more details…”
But on a more serious note, the aim of this mailing was most probably to check an address database. So, whatever you do, don’t reply to stuff like this. In any case, spammers often fake their return address so that all your emotional outpourings are unlikely to reach the right people. And if the spammers do use their real address, any response from you will confirm your account is active and you’ll end up getting much more unwanted mail.

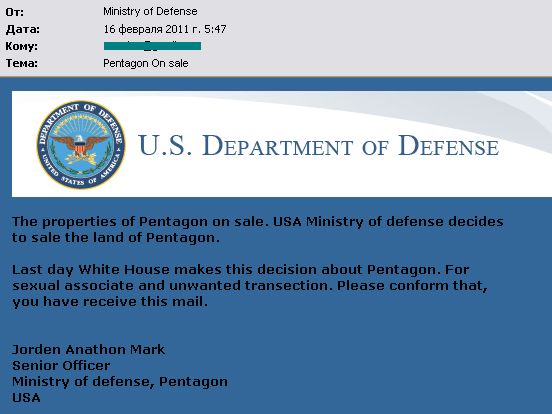



















Pentagon for sale