
It’s a classic type of network fraud: you receive a letter asking you to send the login and password for your e-mail/online wallet/gaming account/etc. If you fail to comply, the phoney “support service” that sent the message threatens to limit or even block your access to the service.
Today our spam traps detected a letter like this in which the fraudsters were trying to swindle users out of out their activation codes for…Kaspersky Lab products! However, that’s not all – they also wanted to know the recipient’s residential address, mobile phone number and credit card number. They only stopped short of asking for the house keys.
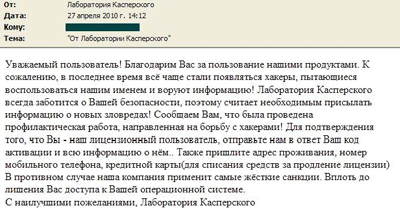
“Dear User! Thank you for choosing our products. Unfortunately, recently more and more hackers have tried to use our name to steal information! Kaspersky Lab always cares about your security therefore we believe it is necessary to inform you about new malware! Please be informed that we have carried out preventive measures aimed at combating hackers! To confirm that you are using our licensed product please send us your full activation code information. Please also send your residence address, mobile phone number, credit card number (in order to pay for a license extension). Otherwise, our company will have to impose severe sanctions, including blocking access to your operating system.
Best regards, Kaspersky Lab.”
Hopefully, our users are not naïve enough to fall for such a primitive scam. There’s no need to explain that Kaspersky Lab would never send out letters like this, especially such threatening messages. It’s nothing more than a crude attempt to obtain some confidential data from some unsuspecting user.
To be fair, the letter does contain a number of true statements. For instance, it states that hackers make use of our name, which they do. And the authors state that Kaspersky Lab cares about the security of its users. That’s also true.




















“I want your clothes, shoes, and motorbike”