
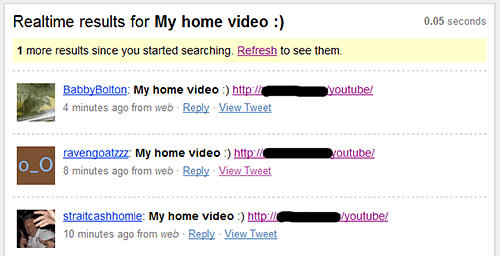
We are currently witnessing a new wave of Koobface messages flooding twitter. The message that is mostly used right now is: “My home video 🙂 <URL>”
The link in infected tweets points to a site with a little javascript.
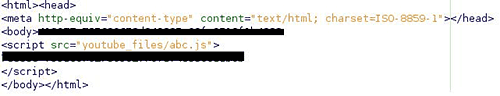
The script calls a php-script on a server which uses an ID to return an IP address leading to the video site. This means the IP address is different for every request.
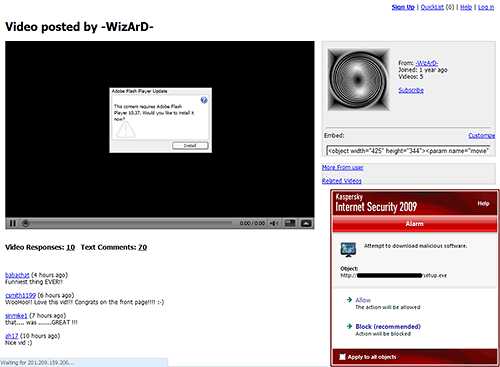
Interestingly, the guys behind this attack are clearly out to maximize their ROI: if you’re using Mac or Linux, you end up getting redirected to an adult site.
Twitter is saying it may block infected accounts. We’re doing our part as well – our users are already protected from the malicious file:
And we’ve also added protection against the malicious tweet itself, which will be detected as Net-Worm.Win32.Koobface.aqy as updates are rolled out to our users.





















Koobface on the tweet