
Every year, the Chaos Communication Congress summons hackers from around the globe, this time again in Hamburg. The four days between Christmas and New year are packed with talks, workshops and events all over the location at the CCH. Large hackerspaces hosts groups and projects from all areas such as lock-picking, art, music, software projects of all kind and more. Tickets were strictly limited this year, so not all who wanted could come. However due to freely available live streams, free access to the video recordings and onsite resources such as Wiki and Communication channels, everyone at any location could join and be part of this event.
It is simply not possible to summarize this event in a few sentences or pointing out highlights without missing some. This also because of the wide range of areas the talks and projects are about. There were technical talks about vulnerabilities in a banking app and flight booking systems. An overview about the North Korean tablet “Woomlin” was given after last years insight into the “Red Star OS” from North Korea. One of the main topics of course is privacy. Others focus on current trends such as IoT Security, BigData and Blockchain. Full program can be found here.
Due to privacy of the attendees, taking photos is only allowed under strict rules. Therefore following impressions do not contain any pictures with people.



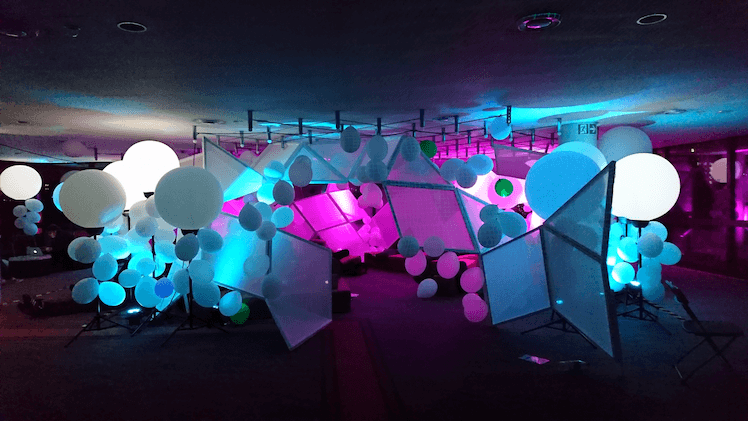























Update from the chaos – 33c3 in Hamburg