
This years DefCon just ended and thousands of hackers, security professionals and other visitors heading back home. This years schedule was again a good mix of talks, but which to attend is not that easy due to the mass of visitors. That’s why the organizers will move again next year to a different location, in order to deal with the growth of participants and events happening.

Five main tracks of talks, skytalks, contests and areas for different interests fills participation schedule for three days easily. Some talks got lots of attention as the experiment by Gene Bransfield, who utilized a cat to map WiFis in the neighborhood, named “Warkitteh“. Hacking airplanes let one quick think of horror scenarios, but, as Phil Polstra stated, it’s not possible to override the pilot. But also attacks on Mainframes were discussed. Mainframes are special systems, mainly used in enterprise and government segement. Several talks focused on hacking connected devices, reflecting the general IoT (Internet of Things) trend.
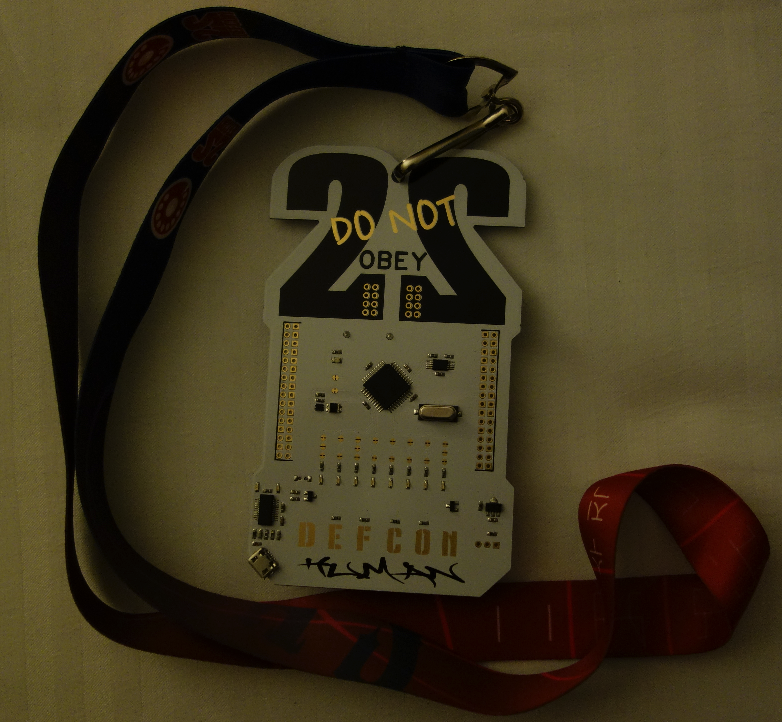
This years DefCon-Badge was again an electronic one, open for hacking and modifying. This ranked from basic to advanced LED/Light-extensions to Quadcopter mounting.



















Warkitteh, Mainframes and planes – DefCon22