
Kudos to our development folks who’ve come up with a public beta version of the interesting KAV Web Scanner, a free service which scans your computer for viruses, and runs directly from a web page on our site.
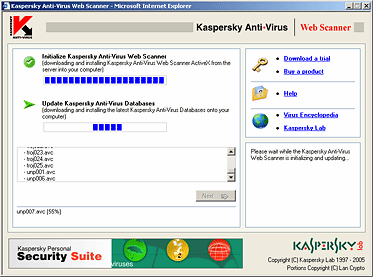
We encourage everybody go ahead and take a look:
http://www.kaspersky.com/beta?product=161744315
Please keep in mind this is not a finished product so we are especially interested in any opinions and/or suggestions you may have. Feedback, queries and (ahem) bug reports should go to: webscannerbeta (at) kaspersky (dot) com
Kaspersky Anti-Virus Web Scanner






















Wim van Grimbergen
Dear Kaspersky,
Our (Para-)Olympic sports club http://www.degrensstreek.nl was hacked 2 months ago and as a result of that now listed on Virustotal.com under Kaspersky as a Phishing site.
Meanwhile the site has been cleaned and completely updated. Can you please remove your phishing results.
Thanks in advance
Wim van Grimbergen
Sportsclub s.v. de Grensstreek Belfeld
Securelist
Dear Wim van Grimbergen,
We sent your request to our anti-phishing specialists.
Securelist team.