
Free WiFi Internet connections are increasingly popular and can be found in hotels, cafes and airports around the world. But it’s not always as good as it seems – although I wouldn’t say TANSTAAFL, some of today’s ‘free lunches’ come with a serious downside.
What makes me say this? Well, earlier today I was catching a connecting flight at Schiphol Airport in Amsterdam. While scanning for available WiFi networks I got the following list:
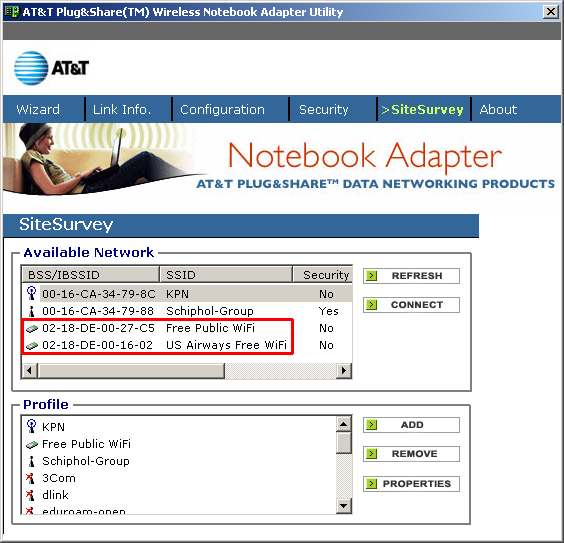
The KPN and Schiphol-Group networks are legitimate but what about the other two?
One thing you might notice is that they’re AD-Hoc type networks. This means that they’re not really WiFi access points but other computers which have been deliberately named ‘Free Public WiFi’ and ‘US Airways Free WiFi’ to tempt users into connecting.
Joining such a network can have a number of unpleasant consequences. If the attacker has Internet access himself, s/he can allow you to get online and then sniff the traffic, potentially getting hold of your passwords and other personal data. And if the attacker doesn’t have Internet access, s/he could try to directly hack your computer by using various network-level exploits.
It’s easy to spot rogue WiFi links – you just need to look for the following signs:
– an enticing name like ‘Free Wifi’ or ‘Free Internet’
– an AD-Hoc type connection, rather than an access point
To stay safe:
– use a VPN link over any public WiFi internet access link to dial back home and access the internet using a secure proxy over the VPN link
– use only encrypted IMAP e-mail connections to read mail, TLS or SSL
– beware of fake certificates
– use a firewall and IPS or a combined security solution such as KIS7
Happy surfing!





















Free Internet