
Life looks good for Brazilian hackers: the absence of a specific law against cybercrime leaves them feeling so invulnerable that the bad guys are shameless about publicizing their thefts and showing off the profits of a life of crime. We showed some of this in a presentation
at the latest Virus Bulletin Conference, and it’s commonplace to find YouTube clips of Brazilian bankers and carders reveling in their ill-gotten gains and rubbing their easy money in the faces of hard-up victims (there’s one example here, and several more out there). It’s also common to find bad guys’ profiles on social networks such as Twitter, Tumblr, etc. Everything is done out in the open, without fear of being caught.
To help new “entrepreneurs” or beginners interested in a life of cybercrime, some Brazilian bad guys started to offer paid courses. Others went even further, creating a Cybercrime school to sell the necessary skills to anyone who fancies a life of computer crime but lacks the technical know-how. On a website dedicated to selling these courses and promoting the “school”, a careful search turns up courses like “How to be a Banker”, “Kit Spammer” or “How to be a Defacer”.

Each course is a well-designed package, with full details of the “curriculum” studied. “How to become a Banker 101” says:
“This course is intended for everybody making online transactions. You will learn how crackers take control of corporate or home computers, what social engineering is all about, how “auto-infect” works, how to use sources (of Trojans), how to manipulate the security plugins installed on browsers such as IE, Firefox, Chrome, Avant, Opera, and antivirus and firewalls. How spamming helps to catch new victims, what “loaders” do and how crackers use them. You’ll learn all the slang used by crackers and bankers and find out about things like “loaders”, “info”, “cc”, “admin”, “laras (money mules)”, “Desco, Ita, Uni, Sta, CEF, BB, City (popular names of Brazilian Banks), and much more. You’ll discover how crackers clone credit cards, checkbooks, IDs, driver’s licenses, birth certificates and other documents. You’ll learn how crackers can own e-commerce websites that store credit card numbers and what they do with this data. You’ll learn about the laws in Brazil and what the sentence is if you’re caught, as well as what risks you run and how to avoid getting caught. All this and much more is part of our course.”
They also offer a course for spammers where you can learn about all the techniques needed to do it effectively. This comes with a gift: a list containing 60 million email addresses to start spamming immediately:

“KIT SPAM UPDATED: Nowadays the virtual world is increasingly competitive, making it hard for new users to compete with advanced rivals in an ever-growing marketplace. That inspired us to create the KIT SPAM, where we include more than 60 million email addresses divided into separate categories: professionals, individuals and companies, executives, businessmen, politicians. The kit includes senders, social engineering techniques to ensure a good spread, extractor of emails and source codes in Delphi. All you have to do is compile and send the mass emails. Everything for R$ 130.00 (around US $75).
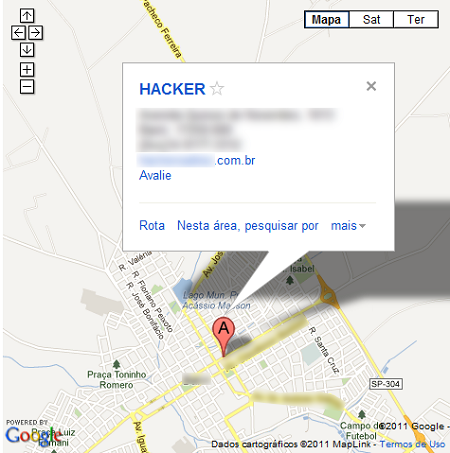
All the courses can be purchased on-line, or if you want, you can watch classes in person. The address of the “school” is also published on the website:
Brazilian financial institutions reported losses of R$ 685 million (around US $380 million) in the first half of 2011 as a result of paying compensation to internet banking clients who lost money. I think its high time Brazilian politicians approve a national law against local cybercrime to enable the police to step up the battle against cybercrime. With the computer criminals publically flouting their ill-gotten gains, we need a more radical and energetic campaign to stop them.
A School for Cybercrime: How to Become a Black Hat





















Kingsley Waike
Its interesting to learn Cybercrime, I find your articles very interesting and educational. I am new in this area and would like to learn more. I have been spied upon by some people listening to my mobile phones and people hacking my emails and making my life hell.
Thank you and may the lord bless you in what you do.
Kingsley Waike
Byser
i wanna be a one of them
Munyaradzi Peter Mutsindikwa
I want to join you
zeehan
i want to be a hacker!!!