
Yesterday, our colleagues from ESET discovered a new version of Stuxnet, which has its driver signed by yet another trusted party – “JMicron Technology Corp.”.
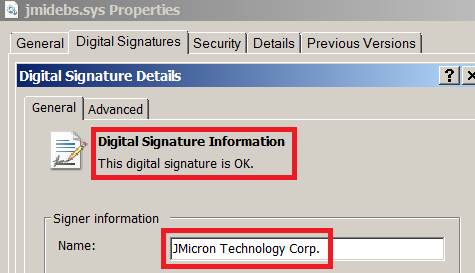
JMicron is a rather well known hardware producer, I’ve myself owned about three or four different computers which had JMicron components inside.
The initial RT certificate was suspicious, but another stolen certificate raises interesting questions.
One possibility here is that both JMicron and Realtek got infected with a trojan such as Zeus, that steals digital certificates. Then, the cybercriminals who got the certificates, either re-sold them on the market or used them by themselves to sign the Stuxnet drivers.
To be honest, the fact that trojans were stealing digital certificates did not really seem that impressive when I have first seen this capability.
Now, coupled with the Stuxnet story, it begins to make sense.






















Stuxnet and stolen certificates