
The wedding of Kate Middleton and Prince William is by far the most popular topic of conversation today. It’s virtually impossible to look at a newspaper or a blog without seeing some mention of the royal newlyweds. And now we are getting in on the act.
And it’s not because we here at Kaspersky Lab take a major interest in the private lives of the British royals. But spammers obviously do – take a look at the offer we received today:
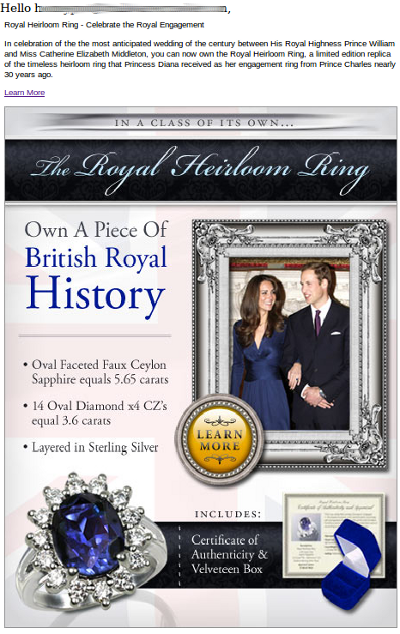
Yes, fake Swiss watches and iPads are so passé – what you need is a replica of Kate Middleton’s engagement ring, originally given to Lady Diana by William’s father Prince Charles. The spammers claim you now have the chance to “own a piece of British royal history”. This royal family heirloom also comes complete with a “certificate of authenticity”.




















Royal spam