
Many websites show different text depending on where the user lives. For instance, home pages of some portals show you the news and weather of your region by default, because you are most likely to be interested in this kind of information first of all.
Of course, spammers and fraudsters also make use of this approach.
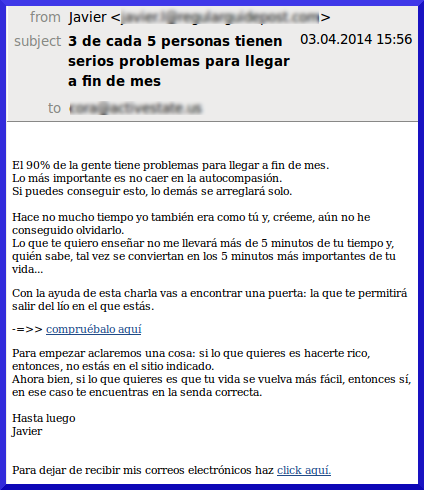
The following letter, written in Spanish, advertises an easy way to earn money online:
The attached link directs users to times-financials.com, registered in October 2013, according to the information on whois:
“Moscow City dad makes $14,000 per month” – says the title.
From Moscow? Hmmm.
Let’s try opening the same site via proxyvpn.se:
Here the dad is from New York.
If you change the language in the address and write EN instead of ES, you can view the site in English:
And if you write FR, you see it in French:
However, if you try a German proxy server, the ‘dad’ will have no idea where he is, and there will be no city name in the title:
The link for these pages is one and the same and leads to yourbinarysystem.com, registered in January 2014. The site promises users wealth beyond their dreams, and yet another link directs to a third site with a standard pyramid scheme.
We haven’t received any letters with links to this ‘dad’ in any other language, except for Spanish. However, we are pretty sure the creators of the pyramid scheme are also sending out letters in other languages to attract attention to their website. If you receive a message like this, please forward it to us!
























The Omnipresent Dad