
The now-notorious arsenal of ‘Nigerian’ tricks has been enriched with yet a new scam.
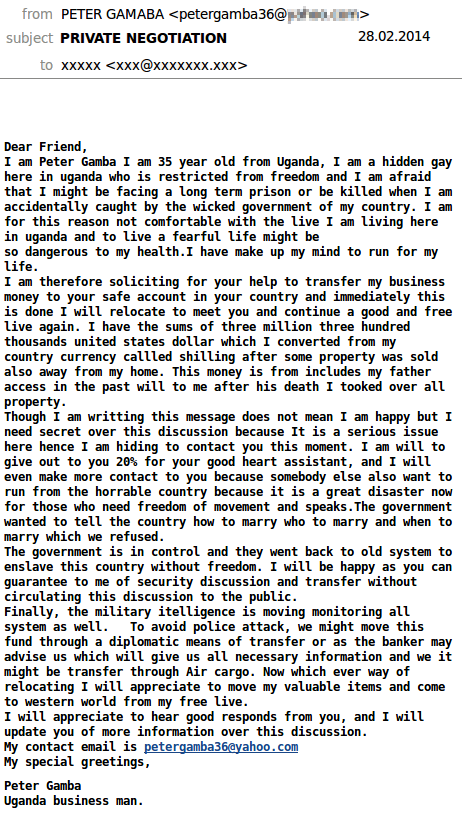
A Peter Gamba (or Gamaba?) from Uganda is asking for help: in his homeland he faces the threat of persecution for his sexual orientation. The sender claims he is threatened with jail or even death. But he has money – $3,300,000. The message then follows the usual scenario – you take his money, put it to your bank account and get 20% of it in return for your help.
Minority discrimination is a very topical issue today (especially in the US where a significant proportion of English-speaking Internet users live). It is almost impossible to avoid this topic and almost everyone has their own opinion on the issue. So the criminals know what they are doing: even if some of the recipients turn out to be conservative champions of more traditional values, there’s bound to be someone who sympathizes with this unfortunate citizen of Uganda facing persecution.
Persecuted widows of overthrown presidents and prime ministers can still be encountered online, though most Internet users are wise to this type of story. This has forced the cybercriminals to look for new ways to arouse sympathy and, of course, greed.
Fraudsters are playing a different kind of card game




















GBluntz
I wish somebody would explain the endgame for this particular con? Assuming somebody responds to them willing to help out, they are then given the task of cashing a $3Mil check and sending most of it back to the dude?? Really??
GordonMcQ
There is no $3M. If you agree to help you’ll suddenly be asked to send him money to cover a never ending series of fictional fees and taxes that he allegedly must pay to release his money, so that you can get yours. It’s called Advanced Fee Fraud – you paying money up front for something you’ll never receive. It basically preys on people’s greed.