
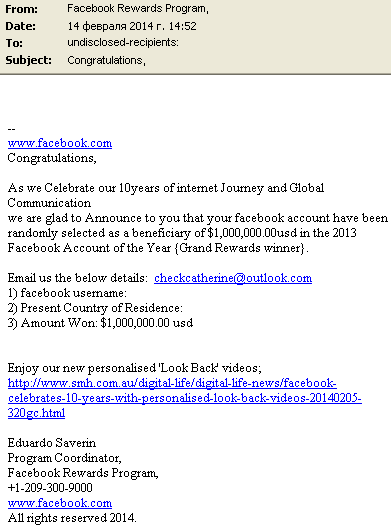
There are plenty of fraudulent messages with the content along the lines of “your email address won a million dollars in a lottery, please contact us to claim your prize”. Internet scammers use this trick to trick users into giving away money: before they can claim their alleged prize the “lucky winners” have to pay tax or a bank charge for a money transfer, etc.
We have now come across an interesting variation of this trick, which involves a Facebook account instead of an email address.
Now, why does Eduardo Saverin (a real person and one of the founders of Facebook) need to know my Facebook username if my account has already won a prize? But an unsuspecting user, blinded by the promise of a huge prize, may not think about that – and that’s what the scammers are counting on.
I’m sure the readers of this blog wouldn’t fall for something like a “Facebook prize”, but our relatives and friends have accounts too, and they may not be so experienced in the ways of online fraud. That’s why they should be warned that such letters are nothing but a scam.
Your Facebook Account Has Won a Prize!




















Leo Morales
How can i claim my reward on my facebook acount?
Kelvin Constant
How can I get my reward, since I was chosen as one of the luckiest people.
Kevin Cochrane
Iv been told that I’ve won money by a Thomas Woodward from Facebook I was wondering how do I claim my money and if this is legit
Claudatious Lane
Is this true
marcus Markussen Wold
Ive just recived a Mail from Facebook that I have won 1 million dollars.
Amanda Morales
agent keger said I was Facebook winner n I was scammed I bought two apple gift cards for $100.00 each n got nothing I want the cash back or my winnings and especially all my info cause now I can’t get back on facebook
Peter Sörensen
I have a winning price for 150.000€ from mark hoffard Facebook over international
Science foundation.
Ich habe viele demands to Zahl vor Lieferung
Ich habe leider über 15.000€ schon bezahlt
Kennen sie diese Muster oder sogar mark hoffard