
In addition to Trojans and Worms, Twitter seems to also be a good platform for distributing rogue security solutions. The latest example of this is a program called “MalwareRemovalBot” which we detect as “not-a-virus:FraudTool.Win32.MalwareRomovalBot.e”.
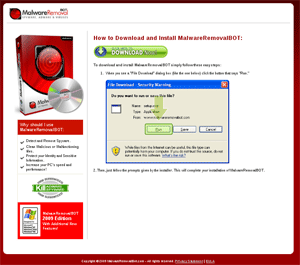
The link in the tweets leads to the ‘vendor’ site – and nearly every link here leads to the download.
The downloaded filename varies – “setup.exe”, “setupxv.exe” or “setup-trial.exe”. It’s a UPX-compressed Windows PE-executable.Once the program’s installed
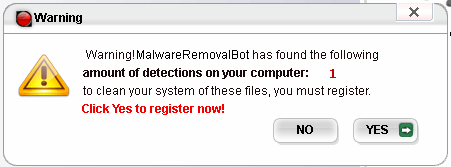
and a scan’s been run, the program may report fake spyware infections to scare the user and get him to “register”.
The registration website leads to the shop where a “special offer” is waiting for the potential customer.
A license for a single PC costs as much as the 3 PC license – $39.95 plus two ‘extra’ technologies for $9.95. The total payment of $59.85 can be made by PayPal or credit-card. Pretty expensive for fake protection.
Conclusion: You can’t expect every tweet to lead to an interesting website, but you can expect that some of them will lead to malicious sites. Use your common sense, and don’t be a twit when you tweet.

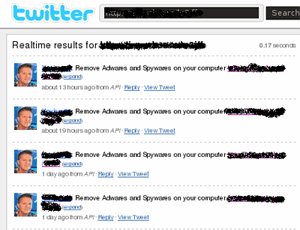





















Rogue anti-spyware on Twitter