
Microsoft is releasing 9 Security Bulletins this month (MS12-008 through MS12-016), patching a total 21 vulnerabilities. Some of these vulnerabilities may enable remote code execution (RCE) in limited circumstances, and offensive security researchers have claimed that a “bug” fixed this month should be client-side remote exploitable, but after months of public circulation, there have been no known working exploits.
The prioritized vulnerabilities patched this month exist in Internet Explorer, a specific version of the C runtime, and .NET framework. The Internet Explorer and .NET framework vulnerabilities may result in a potential drive-by exploits, so consumers and businesses alike should immediately install these patches – mass exploitation is likely to be delivered via COTS exploit packs like Blackhole and its ilk.
When I saw that the Microsoft C-runtime was being patched by MS12-013 for a BoF vulnerability, I was shocked. But it turns out that there is a very limited exploitable delivery vector for Windows applications, and that third party applications statically linked to the C runtime library will not be vulnerable. While folks should be patching this one right away, the vulnerability is not as broad an attack surface as it first seems.
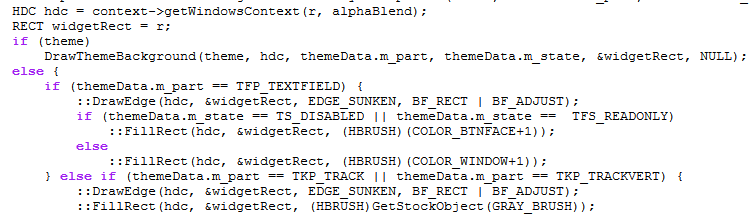
Another vulnerability already receiving much discussion has been publicly known for months now. It is the “GDI Access Violation” vuln patched by MS12-008. This one is interesting because trigger and memory dump analysis have been publicly circulated, along with discussion of how Webkit and other client software “should” be exploitable delivery vectors, but no exploit code has been publicly identified. With the manner in which it was distributed, if it was truly exploitable, it is highly likely that something would have turned up by now.
Please patch your systems ASAP. While the mass exploitation COTS did not include 0day targeting these vulnerabilities, the patches and general information are now public. IT at high value targeted organizations most likely understand that they need to quickly address these, including the EoP.






















Patch Tuesday February 2012