
NetTraveler, which we described in depth in a previous post, is an APT that infected hundreds of high profile victims in more than 40 countries. Known targets of NetTraveler (also known as ‘Travnet’ or “Netfile”) include Tibetan/Uyghur activists, oil industry companies, scientific research centers and institutes, universities, private companies, governments and governmental institutions, embassies and military contractors.
During the last week, several spear-phishing e-mails were sent to multiple Uyghur activists. Here’s an example:
A rough translation:
“The spokesman of the WUC made the following statement about the massacre in Karghiliq country. To the kind attention of everyone.”
It contains a link to a page purportedly on the World Uyghur Congress website. However, the real page link leads to a known NetTraveler-related domain at “weststock[dot]org”.
Here’s the content of the page fetched from that URL:
This simple HTML loads and runs a Java applet named “new.jar” (c263b4a505d8dd11ef9d392372767633). The “new.jar” is an exploit for CVE-2013-2465, a very recent vulnerability in Java versions 5, 6 and 7, that was fixed by Oracle in June 2013. It’s detected and blocked by Kaspersky products generically as “HEUR:Exploit.Java.CVE-2013-2465.gen”.
The payload of the exploit is a file named “file.tmp” (15e8a1c4d5021e76f933cb1bc895b9c2), which is stored inside the JAR. This is a classic NetTraveler backdoor dropper (Kaspersky products block it as “Trojan-Dropper.Win32.Dorifel.adyb”), compiled on “Thu May 30 03:24:13 2013” if we are to believe the PE header timestamp.
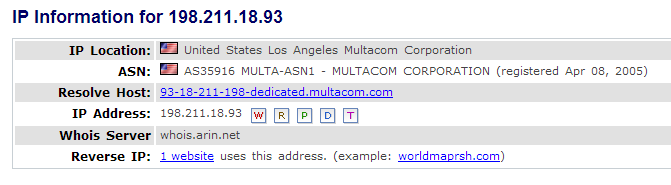
This NetTraveler variant connects to a previously unknown command and control server, at “hxxp://worldmaprsh[dot]com/gzh/nettr/filetransfer[dot]asp”, hosted at IP 198.211.18.93. The IP is located in the U.S., at “Multacom Corporation” and used exclusively to host this C2:
The command and control server is active and operational at the time of writing of this blog, accepting stolen data from victims.
NetTraveler’s Watering Hole Attack
In addition to the spearphishing e-mails, watering hole attacks have become another popular method to attack unsuspecting victims by the APT operators.
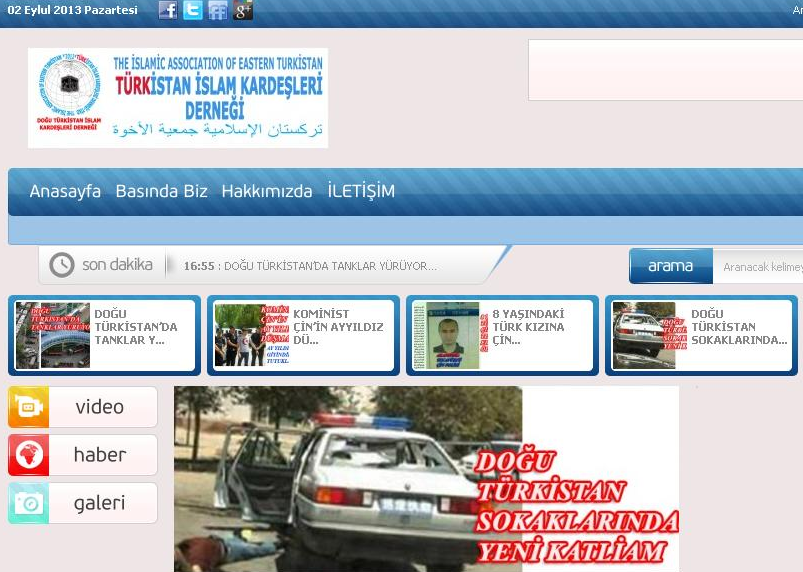
There is perhaps no surprise that the NetTraveler attacks are now using this method as well. Last month, we intercepted and blocked a number of infection attempts from the known NetTraveler-related domain at “weststock[dot]org”. The redirections appeared to come from another Uyghur-related website belonging to the “Islamic Association of Eastern Turkistan”:
A quick look at the site’s HTML code reveals an iframe injection common to malicious websites:
The HTML page on “weststock[dot]org” referenced by the IFRAME contained another malicious applet, named “ie.jar”.
Conclusions
Immediately after the public exposure of the NetTraveler operations, the attackers shutdown all known C2s and moved them to new servers in China, Hong Kong and Taiwan. However, they also continued the attacks unhindered, just like the current case shows it.
The usage of the Java exploit for CVE-2013-2465 coupled with watering hole attacks is new, previously unseen development for the NetTraveler group. It obviously has a higher success rate than mailing CVE-2012-0158 exploit-ridden documents, which was the favorite attack vector until now. We estimate that more recent exploits will be integrated and used against the group’s targets.
Recommendations on how to stay safe from such attacks:
|
1 2 3 4 5 6 |
* Update Java to the most recent version or, if you don't use Java, uninstall it. * Update Microsoft Windows and Microsoft Office to the latest versions. * Update all other third party software, such as Adobe Reader. * Use a secure browser such as Google Chrome, which has a faster development and patching cycle than Microsoft's Internet Explorer. * Be wary of clicking on links and opening attachments from unknown persons. |
So far, we haven’t observed the use of zero-day vulnerabilities by the NetTraveler group; to defend against those, although patches don’t help, technologies such as AEP (Automatic Exploit Prevention)and DefaultDeny can be quite effective at fighting APTs.

























NetTraveler Is Back: The ‘Red Star’ APT Returns With New Tricks