
Earlier, we wrote about the tricks that fraudsters often use on their gullible victims. There’s a prize for you, just pay a small fee to open a bank account (or transport costs, bank fees, overheads etc.), and you will be a millionaire! Sounds familiar, doesn’t it? However, old tricks become stale over time, and readers become alert and suspicious to them. So, the fraudsters have come up with a new variation of an old scam.

Apparently, the fraudsters assume a victim will find it easier to believe in a generous donation from a complete stranger than in a lottery ticket that they have purchased themselves.
Here is another letter in the same vein:
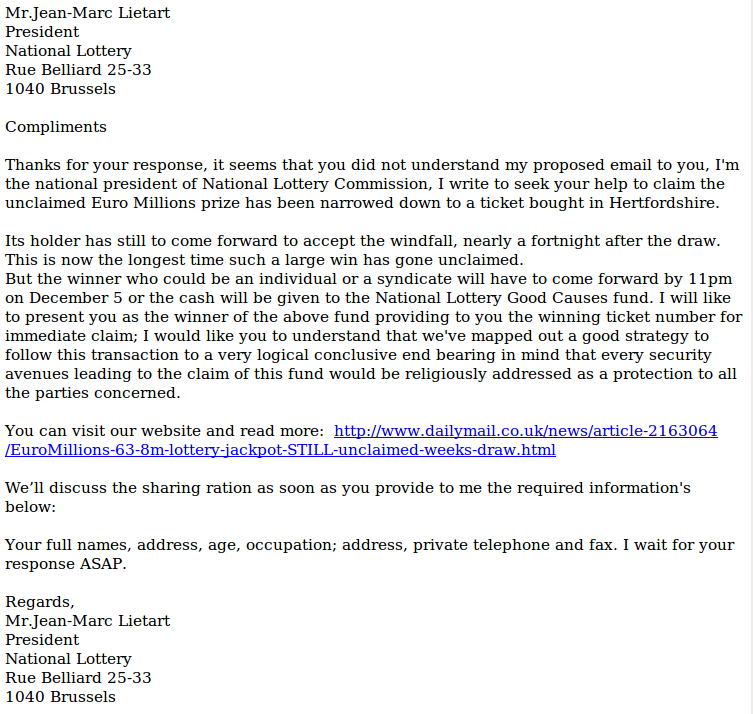
The link in the letter leads to a Daily Mail article which does indeed confirm that someone has won over $60 million in the lottery, but hasn’t collected their money.
Both these letters are strikingly similar to Nigerian scam. The potential victim is not reeled in by the prospect of a cash prize, but is tempted by a donation or a dodgy money-making proposal in supposed partnership with the message writer.



















Lottery fraudsters freshen up their repertoire