
When logging into Facebook today, I was greeted with a new set of controls. In the wake of the apparent success of Google+, it seems that Facebook would like to reassure their user base that they too can control who sees what you post, and who you tag. You can now easily tag who you’re with, where you are, and most importantly; who can see your posts.
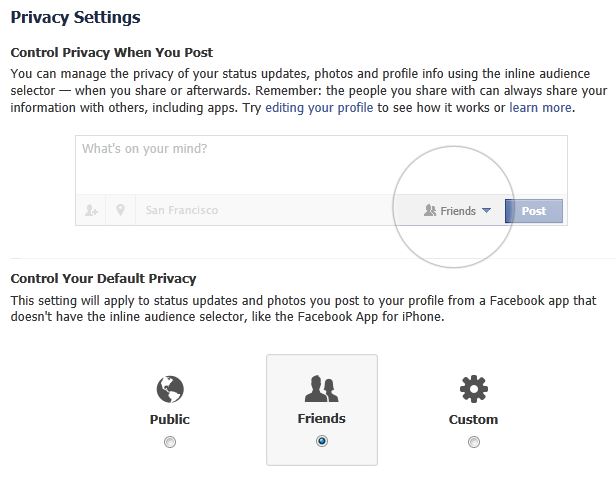
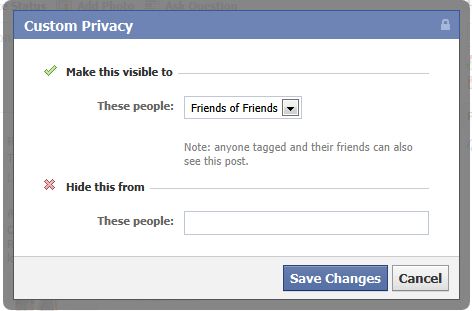
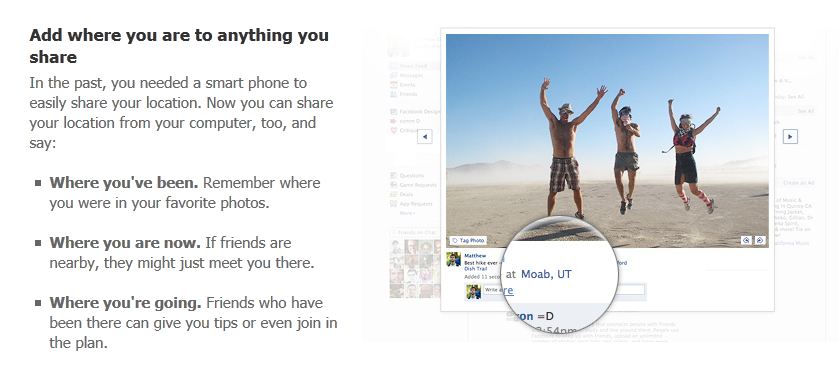
In the Tagging section, you can now choose to approve when you’re tagged before it gets posted. While this is an improvement, you can’t control pictures that are posted of you that are not tagged. Perhaps Facebook will use its facial recognition technology to improve this feature sometime soon. We’d love to see this technology used to protect people. Secondly, with the death of Facebook Places it seems that they’ve changed tactics. They have now added location tagging to posts bringing it right to the front. While you won’t become the mayor of anywhere, it is interesting to see how companies continue to find ways of knowing where you are and packaging it as a convenience to you. The last feature is accomplished through something called the “inline audience selector”. Most interesting here is that you can now not only control who can see your posts, but you can also choose to hide particular posts from particular people.
Tags can also be added retroactively, so now friends, and Facebook can know where you are, and also where you’ve been. In the uproar over location tracking on the iPhone, it will be very interesting to note the success or failure of these new features.
While I feel like overall this is a step forward for Facebook, and its enormous group of users, I can’t help but feel it is long overdue. One has to wonder if Google+ hadn’t arrived on the scene, would we have seen any of these changes?




















Facebook, now with more(?) privacy!