
It’s that time of year again, time to fill out your taxes and pay your part. We’ve seen more than a few examples of Tax and IRS related spam.
Yesterday I received mail with an interesting approach:
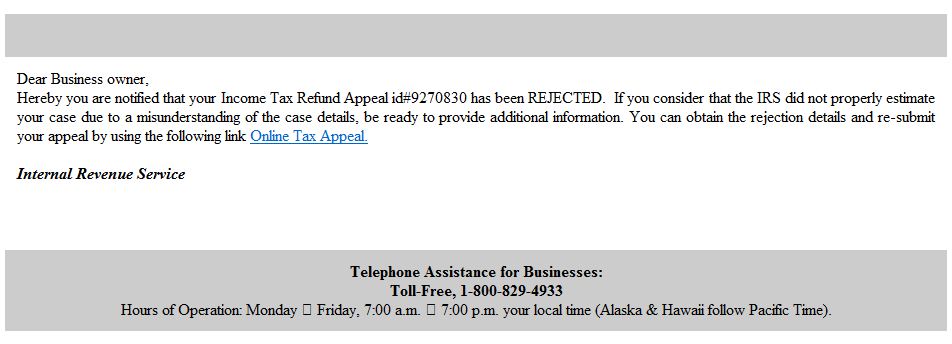
Well, I thought, that’s strange because I don’t own a business, and I haven’t filed my taxes yet. It is somewhat notable how well the email is written. Proper grammar and spelling is attempted, but to a native English speaker it’s not quite right.
When checking out the link, I was first brought to an intermediate page here:
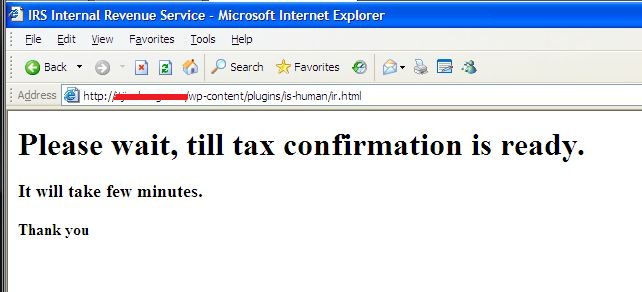
After which nothing happened. The reason that nothing happened is that the javascript that is running in the background is trying to load a web page known for hosting the BlackHole exploit kit. However the page is now down, so the exploit didn’t work. Even if it had successfully reached the page, Kaspersky detected this URL and blocked access:

Please be extra cautious of clicking any links in your email this tax season. If you’re not sure whether an email is legitimate, go directly to the IRS website and start there. Make sure you’re using a quality internet security suite, and make sure to keep it updated. And pay your taxes!



















Here Come the Tax Spammers!