
Dark Market was one of the most famous underground forums ever, for several reasons. The most important one was that one of the administrators was an infiltrated FBI agent running a covert operation that ultimately lead to the arrest of 60 people worldwide. The forum was shut down in 2008, when Dark Market was probably the most important carding forum in the world.
If you work in the IT security field you might already know about this, and also seen some of the nicknames such as Master Splyntr or Max Vision. However, when taking a deeper look on how this forum was forged and the different kind of people involved and how it became the most important underground forum basically consolidating the basis of a new type of cybercrime that we still suffer today is a really interesting story.
I met Mr. Misha Glenny four years ago in Barcelona. I just read his McMafia book and was impressed, so I decided to attend his talk. After a small chat, we discovered to have common interests as he was starting to work in his new book on Dark Market. Of course I was more than glad to collaborate with him from the very beginning, specially with technical support for the odd world of cybercrime and IT security.
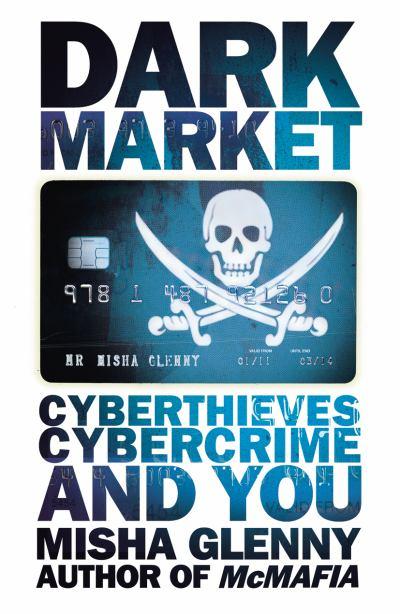
Im happy to announce that now the book is on the stores . I think is really worth the reading, specially the personalities behind the nicknames, the (very different) kind of people involved in such cyberfraud schemes and how they work together.






















Dark Market