
As already reported by F-Secure earlier, criminals are using the Kido/ Conficker hype to bring their rogue Anti-Virus amongst the people. Their solution will sometimes display false alerts on clean systems and try to lure their victims into buying a fake cleaning program for $39.95 from them. Opposed to what they were claiming on remove-conficker.org (website already taken down), their solution fails to detect Kido:
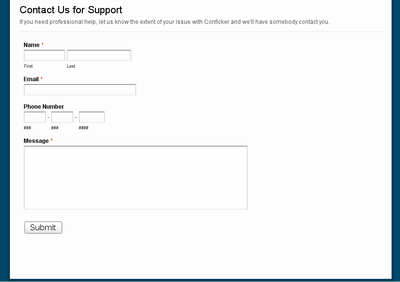
However, these are not the only people trying to make money from public fear of this supposed new mega-worm. Other people for example are trying to sell their assistance in removing Kido from computers on a certain website:
Do not provide them with your real data, there are utilities to help you available for free:
- Kaspersky offers a free removal tool for Kido. You can just download it to an infected machine and execute it to clean it from Kido.
- Felix Leder and Tillman Werner of the University of Bonn have developed a remote Conficker scanner that is able to determine if a system is infected with Kido over port 445 without further impacting the system.
Furthermore, the Conficker Working Group maintains a list of possibly malicious sites abusing the general Kido/ Conficker confusion.





















Criminals Surfing the Kido/ Conficker Hype