
We have discovered a new Tor-based malware, named “ChewBacca” and detected as “Trojan.Win32.Fsysna.fej”. Adding Tor to malware is not unique to this sample, but it-s still a rare feature.
Lately Tor has become more attractive as a service to ensure users- anonymity. Also criminals use it for their activities, but they are only slowly adopting this to host their malicious infrastructure. This capability was added to Zeus recently, as reported by my colleague Dmitry Tarakanov here. In addition, the CrimewareKit Atrax and the botnet-based on Mevade became known because of this.
Introduction
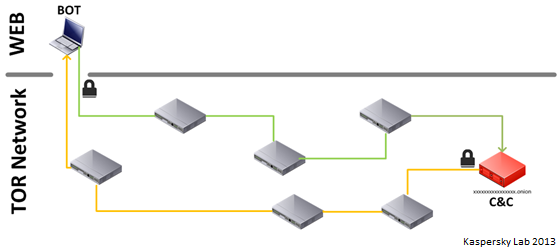
Tor is an overlay network for anonymity. It also serves its own top-level domain, ?.onion, which is only accessible through Tor (of course, there are also Web services routing to Onion-domains from the Internet). This protects the location of a server as well as the identity of the owner in most cases. Still there are drawbacks preventing many criminals from hosting their servers within Tor. Due to the overlay and structure, Tor is slower and timeouts are possible. Massive botnet activity may influence the whole network, as seen with Mevade, and therefore let researchers spot them more easily. Also, implementing Tor adds more complexity.
The Malware
The Trojan (MD5: 21f8b9d9a6fa3a0cd3a3f0644636bf09) is a PE32 executable compiled with Free Pascal 2.7.1 (the version dated 22.10.2013). The 5 MB file contains Tor 0.2.3.25.
After execution, the function “P$CHEWBACCA$_$TMYAPPLICATION_$__$$_INSTALL” is called, which drops itself as “spoolsv.exe” into the “Startup folder” (e.g. C:Documents and SettingsAll UsersStart MenuProgramsStartup) and requests the public IP of the victim via a publicly accessible service at http://ekiga.net/ip (which is not related to the malware).
Tor is dropped as “tor.exe” to the user-s Temp and runs with a default listing on “localhost:9050″.
Once running, the Trojan logs all keystrokes by the user to “system.log”, which is created by the malware in the user-s local Temp folder. This keylogger functionality is installed by using the SetWindowsHookExA-API function with the hook-type WH_KEYBOARD_LL. This system.log is uploaded via [url]/sendlog.php (while the url is hard-coded – see below).
The Trojan also enumerates all running processes and reads their process memory. It contains two different regex (regular expression) patterns to extract information.
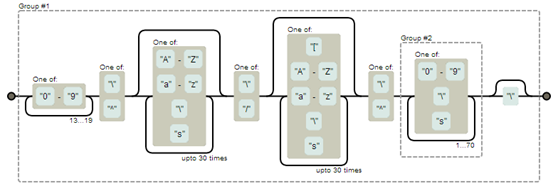
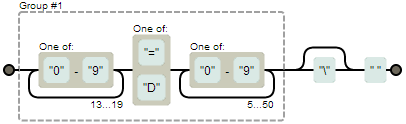
This data is sent using the “Exfiltrate” function, uploading to [url]/recvdata.php The malware also contains an uninstall function named “P$CHEWBACCA$_$TMYAPPLICATION_$__$$_DESTROY”.
Command-and-Control Server
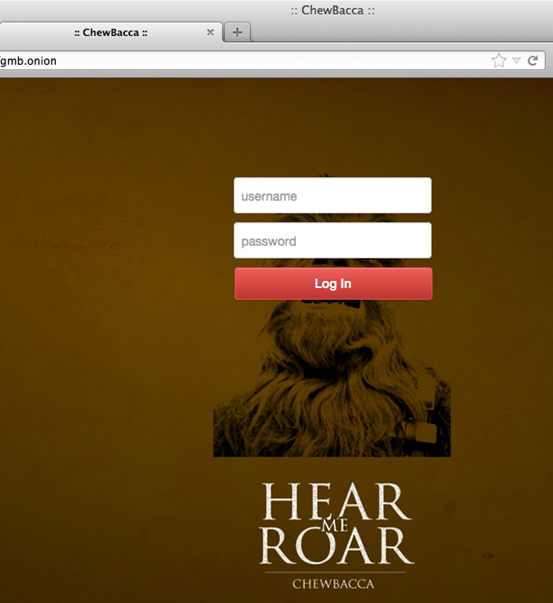
The C&C is a simple LAMP-installation based on Linux CentOS, Apache 2.2.15, MySQL and PHP 5.3.3 (including phpmyadmin 2.11.11.3), hosted at http://5jiXXXXXXXXXXgmb.onion. Opening the URL presents a login interface with the background image of ChewBacca from “A Game of Clones” – a series by Andrew Spear (not related to the malware, of course)
The two above-mentioned hosted php scripts contain the functionality of this server.
- sendlog.php contains the functionality to upload the keylogger-data from the victim-s computer to the server
- recvdata.php is for exfiltrating data v simply called this returns following error message: “Notice: Undefined index: raw data in /var/www/html/recvdata.php on line 24”
Conclusion and Notes
Thanks to my colleague Nicolas Brulez for helping with the analysis.
Chewbacca is currently not offered in public (underground) forums, unlike other toolkits such as Zeus. Maybe this is in development or the malware is just privately used or shared.
It seems that Tor is attracting some criminals to host their infrastructure, as it promises more security for C&Cs v but this holds drawbacks, of course, as outlined above.
ChewBacca – a New Episode of Tor-based Malware





















reza
Where can I download ChewBacca?