
Spammers use all types of tricks to bypass spam filters: adding ‘noise’ to texts, inserting redirects to advertised sites, replacing text with pictures – anything to stop the automatic filter from reading the keywords and blocking the message. Recently, we’ve been seeing a trend to replace Latin characters with similar-looking symbols from other alphabets. This “font kink” is especially typical of phishing messages written in Italian.
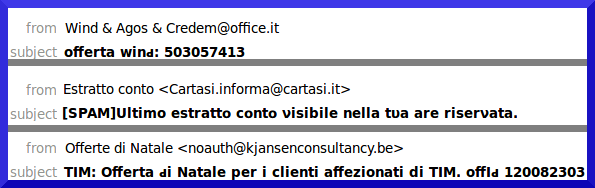
Non-Latin characters are inserted in place of similar-looking Latin characters both in the “Subject” field and in the body of the message. Here is an example of what headers obscured with ‘foreign’ symbols look like:
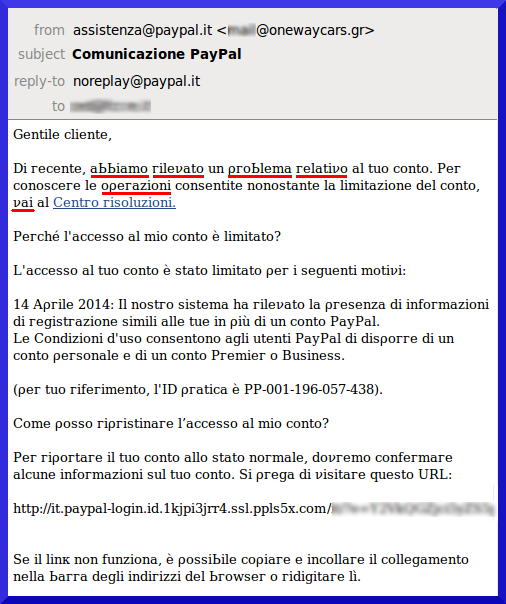
And here is an example of a phishing message using the name of the PayPal payment system and using the same trick. Words containing non-Latin characters are underlined in the first lines; the reader can take a magnifying glass and search for more in the remainder of the text:
Thanks to the UTF-8 coding system, characters from many types of writing systems can be combined within the same email. In the above examples, we saw Cyrillic and Greek characters as well as phonetic (IPA) symbols. Spammers use this as a trick to bypass spam filters. However, the spam filters in Kaspersky Lab products are designed in such a way that they cannot be easily deceived, even if Greek letters or phonetic symbols are used.
Changing characters: Something exotic in place of regular Latin script




















kenneth ridgeway
thank you for information.
Jacob
This is not only something that’s done in e-mails – I see this a lot in blog comments, but it is luckily very easy to block. But, it does make the spam message seem even more desperate and daft than they would otherwise. I wonder what software they are using to blast people’s blogs like this.