
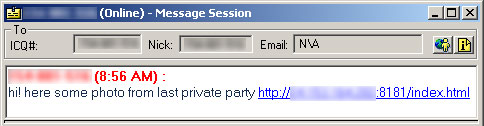
Earlier today, one of our ICQ malware collecting robots was spammed with a suspicious-looking URL:
The machine hosting the page was a home PC located in Herndon, Virginia. The index page on this machine runs a fairly common set of exploits for IE and Mozilla, which attempt to execute Trojan-Downloader.Win32.Harnig.bq.
This trojan downloader is an interesting specimen. At the time we obtained a copy, it was undetected by almost all AV products we tried. My colleague Nikita took it apart and found the following piece of code:
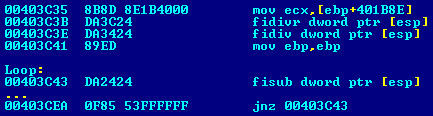
What’s happening here is that after unpacking the FSG outer shell, emulators hit a decryptor which make heavy use of FPU instructions, as can be seen from the snippet of code above. This makes it pretty hard to emulate which explains the low heuristic detection rate.
The first virus to make use of FPU instructions in a decryptor was Virus.DOS.Bashar.670, which appeared in 1997. It will be interesting to watch if this technique will become widespread as a means of avoiding heuristic detection in upcoming malware.






















The link between ICQ, FPU and Herndon, Virginia