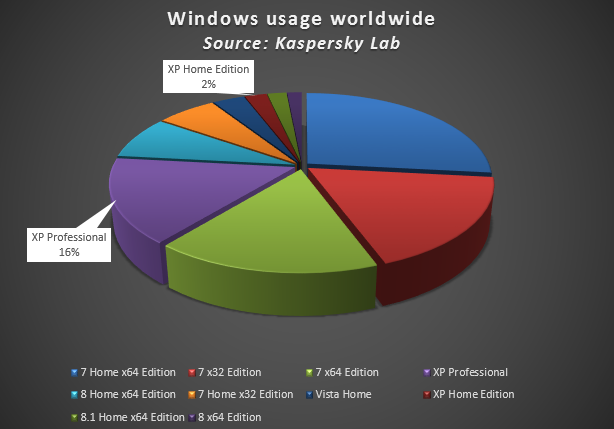
This will take place on April 8, 2014 and Microsoft has already announced this publicly. This would not be a problem if all Windows users would have already migrated to more recent versions of Windows or do so by the mentioned date. However, according to our statistics based on the KSN technology during the last 30 days, 18% of Windows users worldwide still use the XP platform.
What is the problem exactly? Well, initially, with the discontinuation of support for Windows XP, Microsoft will no longer work on updates / patches for the vulnerabilities that appear after the mentioned date. These vulnerabilities will undoubtedly be used by attackers through the creation of exploits to compromise machines. In other words, any Windows XP vulnerability found after April 8th, 2014, will prove effective for cybercriminals and will simply not have an official patch for the operating system. Secondly, once Microsoft’s support for Windows XP ends, other software providers will also stop supporting it in their own products and what will then happen is that users will not only be left with a vulnerable operating system but with third party applications that are also vulnerable, thus multiplying the possibility of infection that will allow cybercriminals to access the confidential information of their victims. In reality, this is a chain reaction that cannot be repaired unless users migrate to a newer version of Microsoft Windows. Finally, since cybercriminals are constantly developing new ways of attack, Anti-Virus companies will also improve their products and introduce new technologies in their newer versions; however, these will no longer support Windows XP either. This is a red alert to Windows XP users for them to migrate their operating systems to newer versions of Microsoft Windows. The best option is to upgrade by installing a Windows system that runs on the 64 bits architecture.
You may follow me on twitter @dimitribest






















The End of Microsoft’s Support for Windows XP