
Some months ago I wrote a blog post called “Rogue AV raising the stakes” which mentioned a new trend in the graphical user interfaces of Fake Anti-viruses. Our predictions were correct, as today my colleague Fabio Assolini found a Web site with an interface very similar to Kaspersky Anti-Virus. See for yourself:

This isn’t the first time we’ve found this kind of fake imitation of our solutions. The interesting part is that during our research we found fake versions of other Anti-Virus solutions on the same malicious host. Can you spot the difference?


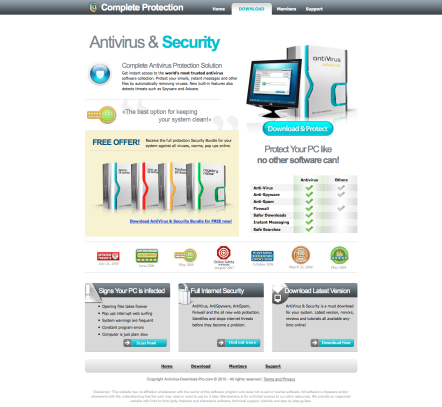

These are just some of the examples. Since some Internet users know what the most popular Anti-Virus solutions look like they can be confused and pay for a Rogue AV solution. This is the main goal of the criminals; to confuse as many people they can, and to get as much money as possible.
On this same malicious server we found 256 different malicious rogue domains with different content but with the same intention: to cheat people by making them pay money for nothing.
Please be careful and always check the domain of the page you’re visiting. Don’t be a victim of criminals!






















Spot the imposter: pretending to be the original