
A couple of months I blogged about how the creators of rogue AV solutions are keeping a close eye on developments in the antivirus market. And my colleague Vyacheslav recently wrote a whole article about rogue AV which highlighted, among other things, the huge increase in this type of malware.
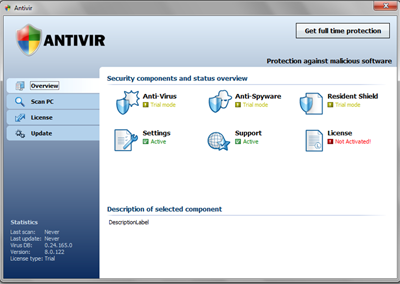
Last week I looked at some samples which showed that the bad guys behind this stuff are ratcheting their efforts up a notch. Here’s the GUI of Trojan.Win32.FraudPack.acji:
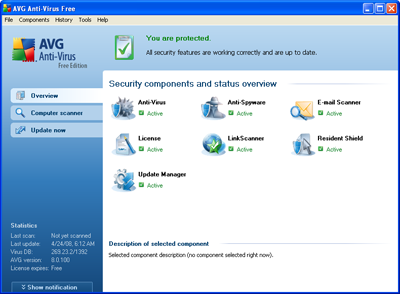
And here’s the product it’s imitating:
There are two points which attracted my attention:
- The interface of the rogue AV is a very close copy of the genuine solution
- The logo isn’t the same, but the rogue incorporates the Windows Security Center logo, and reinforces the perception that it’s a genuine product by using the name of a legitimate free AV solution.
In other words, the rogue AV guys are getting closer and closer to creating exact copies of real AV solutions, at least in terms of the GUI. This makes it much more difficult to determine at a glance whether or not a solution is rogue, for novices and more experienced users alike.
This example shows that maybe we’re not so far from the time when rogue AV solutions will visually be exact copies of legitimate security software. And with the FBI estimating losses caused by scareware at around $150 million dollars, the stakes are getting higher all the time.

















Rogue AV raising the stakes