
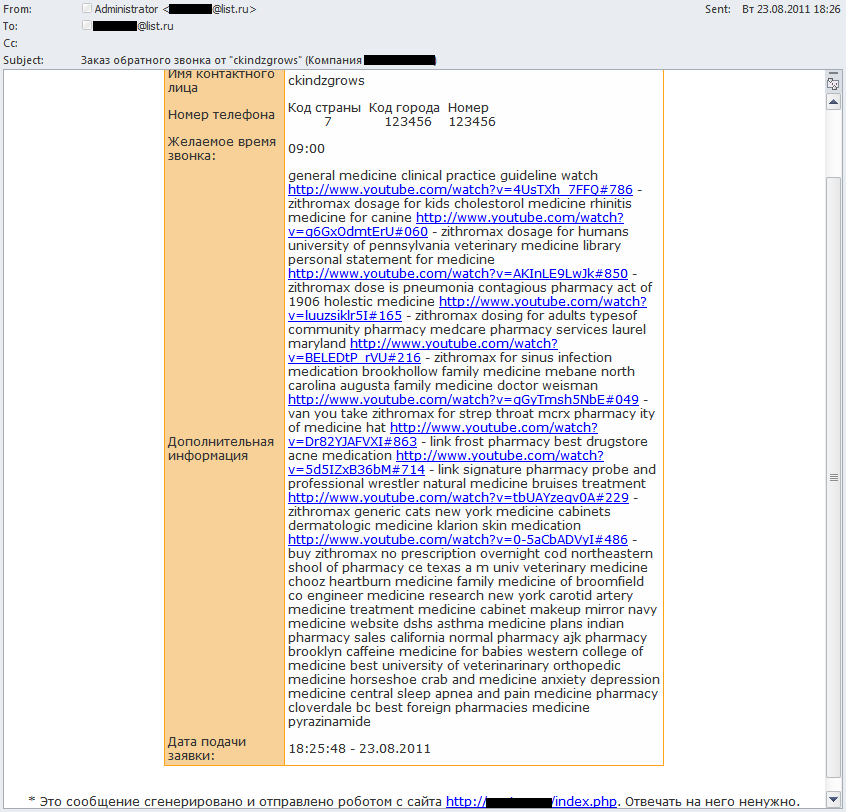
We recently noticed a mass mailing among the general flow of spam that at first glance looked just like the usual “forum” junk mail that appears on forums and bulletin boards, and which are sent as email notifications to users of those forums.
The spam message advertised pharmaceutical goods. However, the links led to YouTube rather than online stores. The videos hosted at YouTube consisted of a background picture with the name of the medication and a link to a pharmaceutical site.
We noticed that the number of views for the different videos ranged from 1 to 40. This once again demonstrates that the response to spam is nowhere near as big as the spammers and their own advertising would have you believe.
I’d like to point out that the use by spammers of YouTube as a video hosting service is nothing new – we first saw it back in 2009. Then, the video promoted spammer services.
When they send out spam like this, the spammers are obviously banking on the popularity of the resource and a semblance of protection from anti-spam filters. In practice, however, the opposite is the case: spammers can’t place lots of videos on YouTube due to the numerous steps that need to be taken to create an account and ensure they are generated by humans. As a result, the number of different URLs in the mailing is very small. This makes it easy for filters to detect the links and explains why this type of spam is not very widespread.
The spammers’ love of YouTube dates back to 2007 when they exploited a vulnerability in the site in order to send spam.
In 2010 spammers offered users the chance to download a YouTube Toolbar that would make it easier to search for videos, but which was actually a Trojan program.
In the first half of this year spammers used YouTube as a cover for their own messages, making them look like notifications from the video hosting service.
The links in the messages led to a pharmaceutical site.
























Spam and YouTube: a long-term relationship