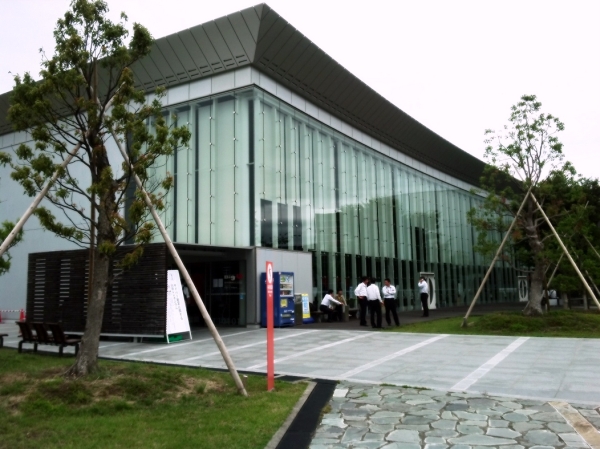
“The 15th Cyber Crime Symposium, Shirahama” with theme “Cloud Security” was held on May 26th – 28th at the “Big U” Information Exchange Center in Wakayama Prefecture, Japan. Approximately 220 people, including government delegates, information security researchers, lawyers, law enforcement and academia attended the event. Experts were presenting about topics like benefits and security risks of cloud computing as well as other related technical matters.
Besides the presentations in the official program, there was also plenty of chance for human networking, with the venue surrounded by beautiful nature and cultural heritage, hot springs and delicious Japanese cuisine.
During the presentations, which were also broadcasted via ustream, tweets tagged with #sccs2011 were shown cycling on a separate screen. This yearly event is targeting Japanese audience and no translation services were offered. If you plan to attend this event in the future, be sure to brush up your Japanese, it most certainly is worth it. Past content of the same event covered themes like “Threat of Malware/Virus” (2009) and “How can we protect the children and ourselves from harmful contents” (2010).



















Shirahama Symposium 2011