
This year’s 17th Association of anti-Virus Asia Researchers international conference, “AVAR 2014” came back to Sydney, Australia with the theme “Security Down-Under”. The event was held here also in 2003.
The arrival hall at Sydney airport did indeed look like this:
More than 170 attendees related to the anti-virus industry, CERTs, law enforcement and academia from around the world had plenty of opportunities to network and exchange thoughts and ideas.
The keynote, delivered by Graham Cluley, included a part where everybody was invited to join in singing “The anti-virus industry song”.
The presentations covered subjects like the current global anti-malware ecosystem, the mobile cybercriminal underground market in a certain country, details about the Dragonfly threat actor and much more (see the link below for more information).
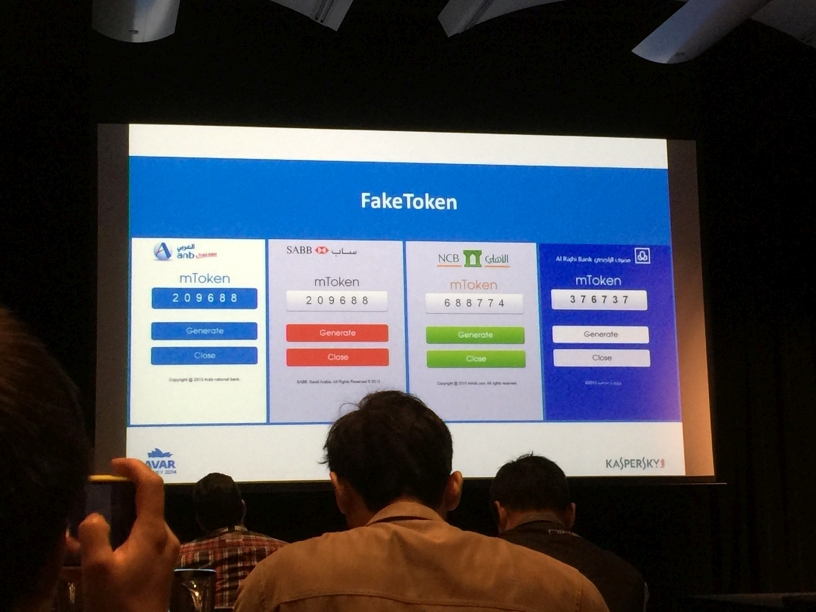
Kaspersky Lab’s Roman Unuchek did present his research about Android banking botnets.
Colleagues from ESET did a great job organizing not only the conference but also an entertaining gala dinner at the “Power House Museum”.
Another highlight was the “after party” in a Bavarian Beer Cafe. That turned into a kind of power house as well when some attendees of the AVAR 2014 got on stage and rocked the place.
Last but not least there was also an opportunity to see a bit of Sydney’s scenery and wild life during a tour.
We are looking forward to the next AVAR in 2015, which will be held in Vietnam.
Event site: http://www.avar2014.com/ehome/index.php?eventid=83858&
AVAR 2014 – Australia


























Campbell
Upside down picture ? Witty !!! But I guess thats Koala Diplomacy…..