
The eighth annual Counter-eCrime Operations Summit (CeCOS VIII) was held in Hong Kong on April 8th , 9th and 10th, 2014.
The event brings together global leaders from financial services, technology, government, law enforcement, communications sectors and research centers.
Cybercrime fighters from the field examined:
- Public-source criminal tracking techniques
- Cloud and mobile malware forensics
- The latest crimeware and web-based attack schemes
- Bitcoin as a cybercrime tool
- Globalized industrial cybercrime event data sharing
- Ransomware scams menacing businesses
- Global approaches to securing the Domain Name System
CeCOS VIII was an open conference for members of the electronic-crime fighting community. The agenda is located at http://apwg.org/apwg-events/cecos2014/agenda and I had the opportunity to share recent research results on the second day of the event.
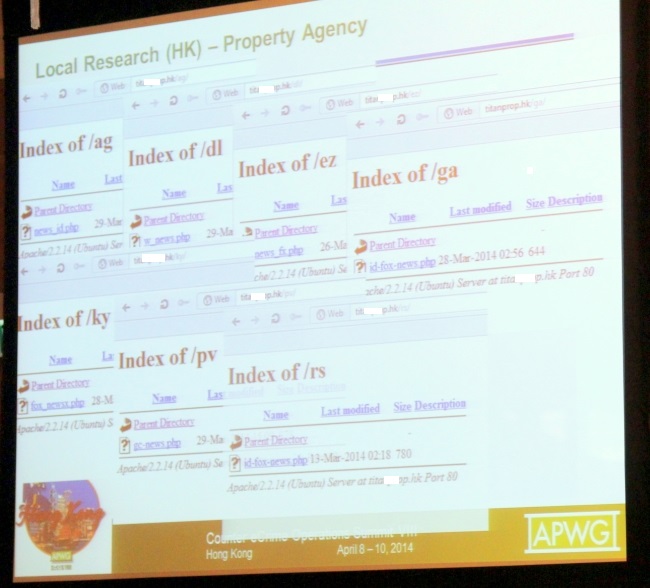
My topic was the broad global abuse of compromised websites for malicious purposes.
After showing plenty of samples of such problematic websites in Japan, I went on to highlight local .hk samples and exposed samples related to the recently discovered “AOL spam” problems, namely compromised domains redirecting to diet scams or ‘housewife-make-money-from-home’ scams.
We had been seeing these suspicious URL patterns since the end of February 2014 and took measures to detect related data as “Trojan.JS.Redirector.acf” as well as heuristically.
More information about this threat can be found at virusbtn.com.
This Year’s CeCOS VIII included about 130 attendees from around 20 countries. The organizer noted: “In some dimensions, this is the strongest operations program we have ever organized. I know that important developments will proceed from CeCOS VIII and make enduring contributions.”
I can only confirm that there were plenty of opportunities for discussions and networking and it was a fruitful event – as usual, I may add.























CeCOS VIII – Hong Kong