
It was nicely crowded (~550 people) and more than 40 speakers from around the world shared their work on a nice variety of different topics.
We attended only the two-day conference part of the event, which also included a hands-on “HITB LABS” section, a “Capture The Flag”(CTF) battle …

and a “Lock Picking Village”, amongst other things.

Andy Ellis (CSO, Akamai) started the first conference day with his keynote speech, “Cognitive Injection”. He illustrated some interesting examples of how human perception can be tricked using the simplest techniques. The audience had to observe very carefully certain details of his “mini-demos” in order to spot unexpected events.
Due to all the observing, I noticed Andy’s “shoes”; something seemed different:

The secret was revealed when I approached him after his presentation to take a closer look. He was wearing some finger shoes, which looked very comfortable.

During the day, several very interesting presentations took place. I won’t go into too much detail here as the full content is available on the event website, but here some random picks:
Dr. Marco Balduzzi, Kyle Wihoit and Alessandro Pasta presented impressive research about Vessel Tracking Systems.
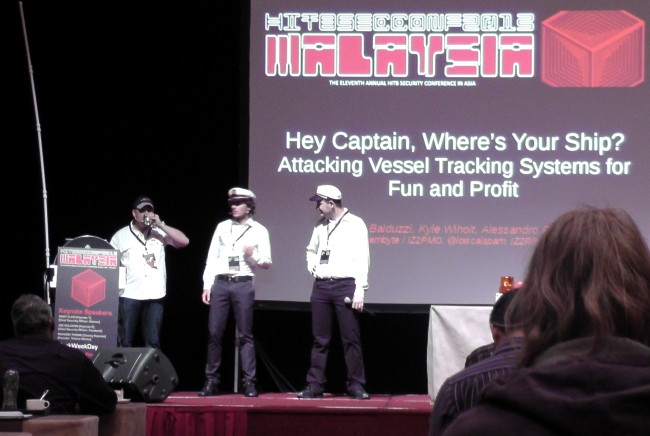
They showed how to manipulate data transferred by the Automatic Identification System (AIS) in order to create fictional vessels or alter positional data of real ones.
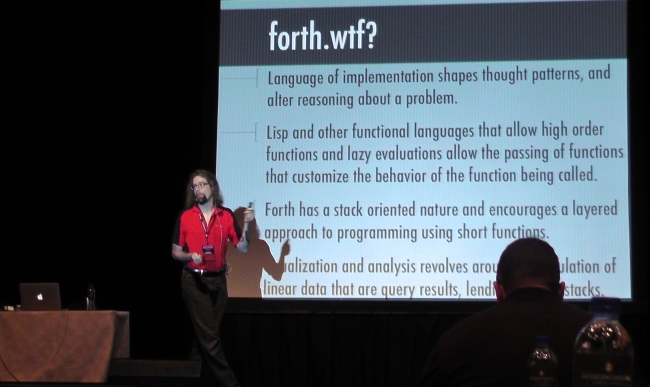
Wes Brown demonstrated an approach to “Visualization to Analyse Malware” with “FORTH”.
Slightly unrelated: During the idle time in between presentations, I noticed some Japanese characters on the monitor of a possible Pokemon fan in the audience.
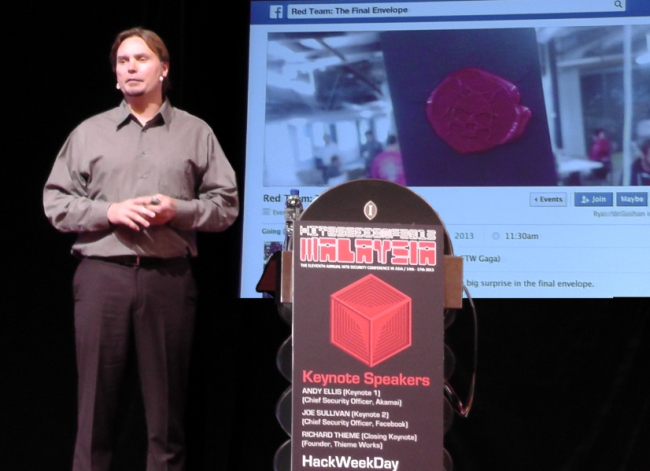
The second day began with the keynote speech of Joe Sullivan (CSO, Facebook), sharing some recent examples of innovative security initiatives that leverage social engagement to improve security.
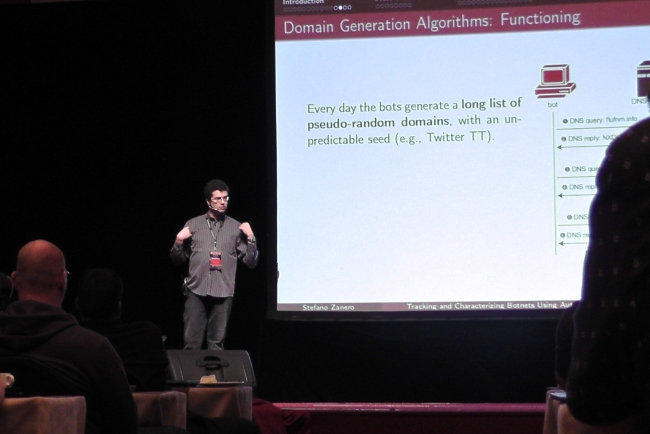
Stefano Zanero introduced “Phoenix”, a system to analyse domain names in order to discover and categorise automatically generated domains.
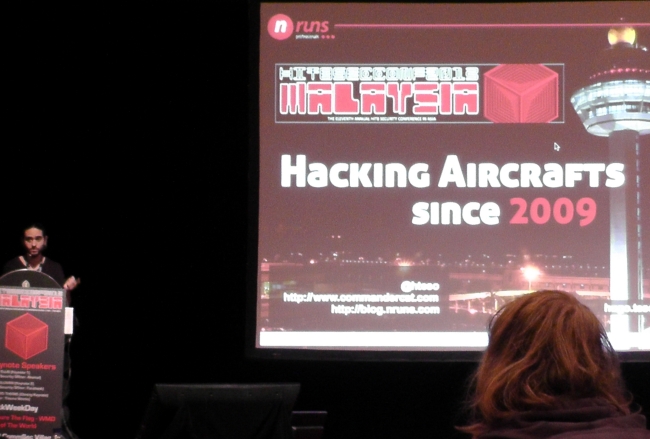
And another highlight for me was Hugo Teso discussing issues in the Aviation Security field. He seemed able to modify approximately everything related to the navigation of an airplane due to lack of proper security implementations in several different systems.
Finally, there was this lady

I don’t know who she is or what she does but I’m sure she’s good at it.
As already mentioned, the event was “nicely crowded”. And that is one of the points I like very much: We were able to attend any part of the three track program without queuing in endless lines long before begin.
The event staff was very kind and friendly, as always, and we had a great time during and after the official program. Thanks very much guys!




















Hack In The Box 2013 KUL