
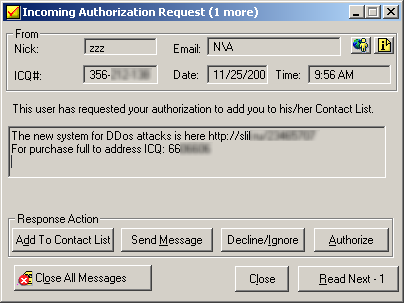
Messages like this have become a common sight in our ICQ spamtraps:
If you are wondering, the cost to DDoS a website can range between 100$ and several thousand US Dollars. For www.viruslist.com it would be around $3000 per day. Apparently, there are even special discounts for “DDoS multiple sites” packs – “buy two, DDoS the third for free!”. They even offer different methods to DDoS a website – for instance, syn flood or heavy traffic. This is because some ISPs charge by traffic, and several hundred GBs of extra traffic can cost the website owner a lot more than the DDoS attack.
Faced with a massive DDoS attack, many companies simply remove their websites from the net until is attack is over. Others pay up the ransom, if there is one. The best thing to do is to work with the ISP and companies specializing in blocking DDoS attacks. Please don’t pay the ransom, it only encourages the bad guys to carry on.






















Saturday morning specials