
Last year when we were in Dubrovnik, Croatia, I made a WiFi study. The statistics I obtained showed quite a dangerous situation regarding security in the local WiFi networks. In many cases the network traffic wasn’t encrypted at all and susceptible to a data leak.
One year later the subject of WiFi security is even more apparent. If you remember, the Google Sniffing beta recently made their own study, and my colleague Costin Raiu wrote a blog post about it, giving important security tips to protect yourself and your network from intruders.
This year our Security Analysts Summit takes place in Limassol, Cyprus. So, I decided to see what the local WiFi security situation is, and what the Google Sniffing beta would find if they performed it right here.

Aside from the beautiful views (you can see in the picture above) we can say the following:
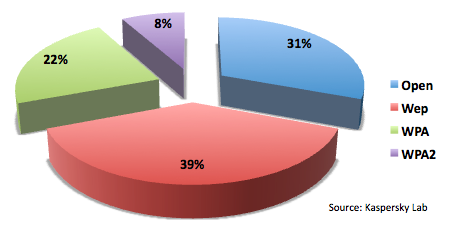
Security:
31% of all WiFi networks don’t have any traffic encryption. In other words, those networks are extremely dangerous as criminals could easily intercept sensitive information such as passwords, pins, and other personal details.
39% of all available networks utilize WEP encryption, but it has been known for quite some time that WEP is not secure since it can be broken in just a few minutes.
Finally, just 8% of all WiFi networks are actually protected, since they implement the WPA2 encryption protocol.
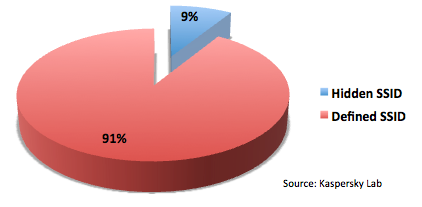
In some cases the owners of the access points try to protect their networks by disabling the broadcast of the SSID. This cannot be
considered as an additional safety measure, as some creative offensive security techniques can quickly reveal the SSID. 9% of available WiFi networks implemented such security.
Physical layer:
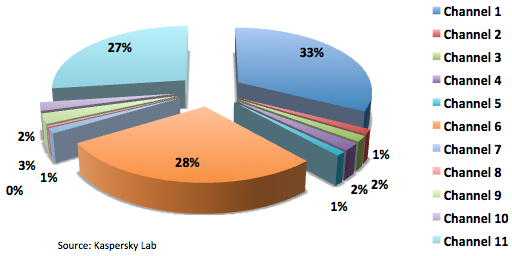
The most commonly used channels by AP owners are 6 and 11 (since they are used as a default setting by many AP vendors). Another commonly used channel is number 1. This trend seems to be a reflection of one of the local ISP providers. It appears that the provider uses this channel for their customers.
We’d like to encourage all users to consider WiFi security seriously. In addition to the recommendations given already, I’d like to add that sometimes it’s also useful to enable MAC address filtering for connections to the Access Point. If you work in a very hostile environment, you can also compliment your security with a Captive Portal over SSL.
SAS2010: Wardriving in Limassol, Cyprus




















Badmojo
Nice one, yes most networks are as is untouched, just like they were provided in the initial setup. Even though this study is quite old now, still not much has changed since then.
That purely points to how much awareness is made for networking in Cyprus.
On the other hand criminal activity on networking in Cyprus is so little that it could barely make any news headlines.
Still great study.