

Last month, we were over in Dubrovnik for our 10th anniversary Virus Analyst Summit: five days of presentations, brain-storming, research and interviews. At around the same time, my colleague Christian’s article on the dangers of using WiFi networks on holiday was published.
Dubrovnik was full of tourists, as well as all the summit participants and journalists we’d invited, and most people were probably checking their email, using IM, or surfing social networking sites on a regular basis. With this in mind, I decided to do a bit of war-walking to check the security of the town’s networks.
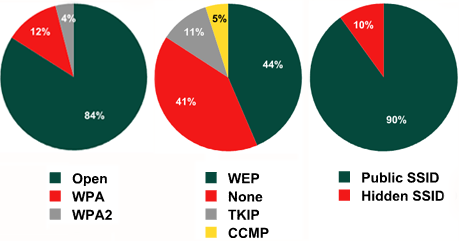
A few days walking the narrow streets of the old town resulted in the following data:
- 84% of networks didn’t use any type of authentification
- 41% of networks didn’t use any type of encryption, meaning that any data (including confidential information) could easily be intercepted
- 44% of networks used WEP encryption, which isn’t much better than no encryption – WEP can be cracked in a matter of minutes
- Around 10% of networks hid the SSID in order to increase security
It’s not surprising that so many of the networks were completely open; Dubrovnik is a tourist town, so a lot of cafes and bars offer free Internet access with the aim of pulling in more customers. These open networks are a classic example of the trade-off between security and usability: although easy-to-use free Internet access seems attractive, the security risks are far higher than those associated with secure networks.






















War walking in Dubrovnik