
Once again, there’s a new wave of Koobface.
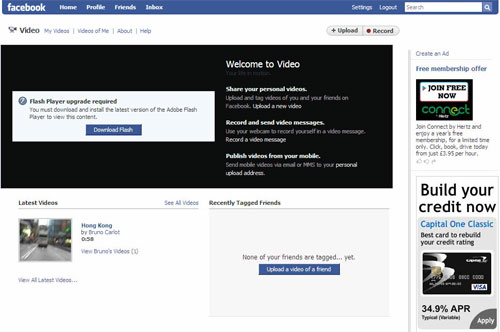
But this time, the tactics have changed. There’s a new twist to the social engineering, with links from infected messages leading to a very well designed Facebook lookalike page (far more convincing than the previous YouTube page)
And Koobface is now sending unique tweets. Messages sent in previous attacks were all the same:
“My home video 🙂 [URL]”
Now there’s a random component being added, with strings like “HA-HA-HA!!”, “W.O.W.”, “WOW”, “L.O.L.”, “LOL”, “;)” or “OMFG!!!” at the end of each tweet, so the malicious tweets look like this:
They are also adding a random component to the Koobface landing page so now, the URL gets shortened to a different bit.ly URL each time (see my post about the dangers of short URLs) making it harder for Twitter to filter and delete infected messages.
i.e. http://u*******.se/pub1icm0vies/?[RANDOM] -> http://bit.ly/[RANDOM]
This week everyone’s been talking about how Twitter started to use the Google Safebrowsing API to block tweets containing malicious URLs. It is definitely going to stop some attacks, but as we’re seeing with the current attack, it won’t eradicate the problem completely. It’s clearly a step forward, but a single swallow doesn’t make a summer.
We detect the malicious binary as Net-Worm.Win32.Koobface.d and the script that is doing the redirect on the landing page as Trojan-Clicker.HTML.IFrame.ob.
Currently we’ve identified almost 100 unique IP addresses hosting Koobface. We’ll keep you posted!
UPDATE: We’re working on getting the main Koobface page taken down.






















New tricks for Koobface