
As we discussed not so long ago, short URL services are becoming more and more popular among social networks. And the recent event when such a service got compromised highlighted the sensitivity of the problem.
We decided to take a look at just how popular each of these URL shortening services are on Twitter. So we’ve collected all the URLs from the public timeline and thought it would be nice to share the results with the world. The stats are based on data collected during a 24 hour period.
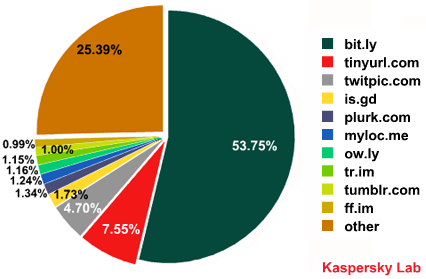
As you can see, more than half of the URLs posted on Twitter belong to bit.ly, making it the winning service with 53.75%. Tinyurl.com is in 2nd place, but with only 7.55%, there’s a big gap between this and 1st place. Twitpic.com accounts for 4.70% of all URLs tweeted, but as it isn’t actually a URL shortening service, just an image hosting website for Twitter users, we can’t in all good conscience count it among the top ranked services. So is.gd is the last in the top 3 – with just 1.73%.
What’s really worth noticing is that more than half of the URLs being tweeted every day are hosted by a single service, bit.ly. But with great power comes great responsibility – if this service got compromised, that would mean more than half of the URLs circulating every day on Twitter would be compromised.
As I have security in mind all the time, I would be a lot happier to see a more even spread across URL shortening services without such a clear leader.





















Twitter short URLs: statistics