
It’s the same every year: as soon as Valentine’s Day gets close, all the spammers concentrate on this event to spread unsolicited mails – sometimes with malicious little gifts.
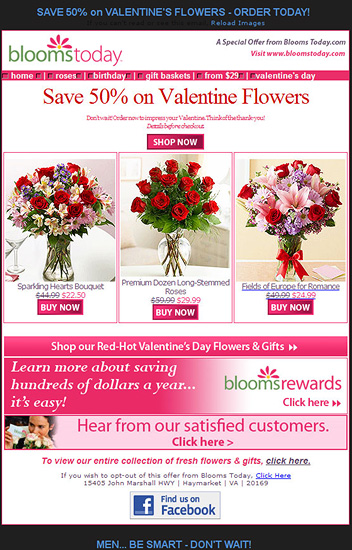
An alltime favorite gift when it comes to Valentine’s Day: flowers! This spam offers great savings when you buy flowers, but tries to trick you into a subscription, where you’ll get charged $9.95 every month via your credit card. Make sure you don’t fall for it!
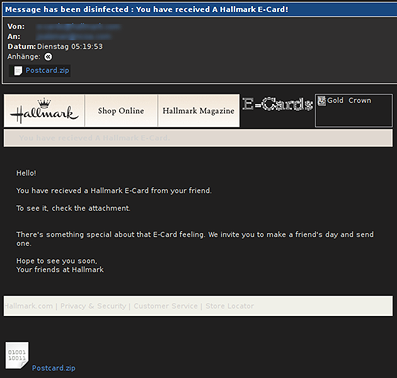
But even worse than this are mails with malicious greeting cards. The number of cards sent always goes up around international festivals like Valentine’s Day. The sender usually just wants to entertain friends and relatives and make them happy. But the cybercriminals only use them for financial gain – from your money! We’ve intercepted spam which allegedly originates from Hallmark, a major supplier of greeting cards for every occasion. But in this case something’s happened to the message – this sample includes malware. We detect the malware as Trojan.Win32.VB.rso (this offers an attacker remote access to your system, and will also send further spam) and P2P-Worm.Win32.Agent.ez.
With Valentine’s Day just round the corner, we’ll all probably be getting a lot more spam like this.
And with more than 30,000 new malware samples appearing every day, make sure you’re protected by following the usual simple rules: keep your antivirus solution up-to-date, be cautious if you get email from an unknown sender, and make sure not to open any attachments.






















Need a Valentine’s gift?