
During 11-12 October, the “Information Security Workshop in Echigo-Yuzawa 2013” took place in the Echigo-Yuzawa, a location that is famous for its hot springs. About 300 people attended the event. Among attendees were security specialists, malware researchers, police officials, government officials and prominent professors. 15 college students also participated in the event as operational staff.

The conference was full of good presentations. To name some of them: Masakazu Takahashi (Microsoft), presented “Past and Future of Information Security that Look Back to the Opportunity Windows XP / Office 2003 End of Support”; Eiichi Moriya (Centre for Business Information Ethics, Meiji University/IBM) talked about “SNS Information Security and Rules”; and Hiroki Iwai(Deloitte Tohmatsu Risk Services) introduced “Challenges and Prospects of Forensics in Cyber-Attacks”.

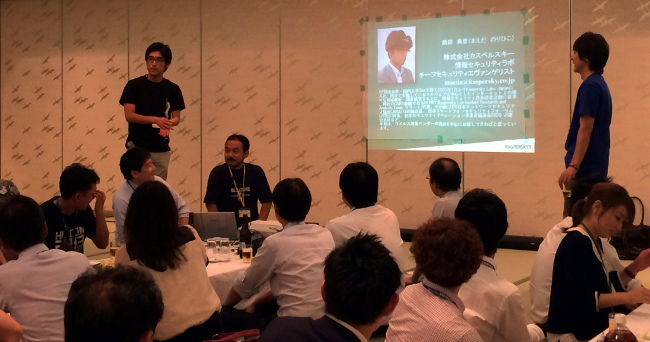
The most interesting part was the night session – a closed panel discussion over some drinks and nice food. Participants were divided into several groups, in accordance with the topics they were interested in.
The topic of our room was how we respond to incidents. For example, should we disconnect from the LAN or stay connected when we find an infected host? Most of the people believed it was better to disconnect it as soon as possible. On the other hand, a few researchers insisted that keeping the connection and logging an attacker’s activity was important.
It was the hottest discussion of the night. Norihiko Maeda, Security Evangelist of Kaspersky Labs Japan, was one of the panelists.
It was a great opportunity to meet key people in IT security, as well as to exchange information and opinion on cybercrime in Japan. I would recommend you to join the event if you are interested in security – and speak Japanese 😉




















Information Security Workshop in Echigo-Yuzawa 2013 (Japan)